Device certificates perform three main functions:
- Ensure that the 8x8 Virtual Office service is communicating with your specific, unique endpoint over the Internet so no...
- Ensure that the communication to your device is secure at both ends, and a hacker cannot intercept passwords or customer...
- Make activating your device easier with automated provisioning and simple...
How does the device CA certificate work?
The device CA certificate can sign other certificates. The IoT Edge Security Manager generates the workload CA certificate, the first on the "operator" side of the process, when IoT Edge first starts. This certificate is generated from and signed by the device CA certificate.
What is the difference between device certificate and client certificate?
The client certificate is intended to authenticate users in public-facing channels whereas the device certificate, which authenticates your device, is intended to be used only on your internal (private) network. Secure authentication through the use of verified organizational identity,
What are the benefits of device certificates?
Device certificates are extremely flexible and can secure a wide range of IoT devices with different utilization and complexity. IoT security certificates help you scale device security across multiple networks and geographic regions. Device certs are easy to implement and manage.
How do device certificates get signed?
Sometimes the end user, or operator, of a device purchases a generic device made by a manufacturer then manages the certificates themselves. Other times, the manufacturer works under contract to build a custom device for the operator and does some initial certificate signing before handing off the device.
How do machine certificates work?
Also known as computer certificates, machine certificates (as the name implies) give the system—instead of the user—the ability to do something out of the ordinary. The main purpose for machine certificates is authentication, both client-side and server-side.
How do security certificates work?
The certificate is signed by the Issuing Certificate authority, and this it what guarantees the keys. Now when someone wants your public keys, you send them the certificate, they verify the signature on the certificate, and if it verifies, then they can trust your keys.
How do I check my device certificate?
Select “Settings” from the menu. Scroll down to the “About” section. Under “Play Protect Certification,” it will say whether your device is certified or uncertified. That's it!
What is Device Identity certificate?
In a nutshell, device certificates enable the following: Secure authentication through the use of verified organizational identity, Device identity via the common name registered on the certificate, Data security through the use of encryption, and. Data integrity through cryptographic signatures and hashing.
What are security certificates on a phone?
Digital certificates identify computers, phones, and apps for security. Just like you'd use your driver's license to show that you can legally drive, a digital certificate identifies your phone and confirms that it should be able to access something.
Where are certificates stored?
Every certificate on your business computer is stored in a centralized location called the Certificate Manager. Inside the Certificate Manager, you are able to view information about each certificate, including what its purpose is, and are even able to delete certificates.
What happens if I delete all certificates?
Removing all credentials will delete both the certificate you installed and those added by your device. Go to your device Settings. In Settings, navigate to Security and Location. This is usually at the bottom of the application.
What are user certificates used for?
Of the three general types of certificates found in a Windows PKI, the user certificate is perhaps the most common. User certificates are certificates that enable the user to do something that would not otherwise be allowed. The Enrollment Agent certificate is one example.
Why does my phone say network may be monitored?
The warning/notification you are getting happens when a security certificate is added to your phone (either manually by you, by another user, or automatically by some service or site you are using) and it is not issued by a pre-approved (by Google) issuer, then Android's default security setting is to display the ...
Why do I need security certificates on my phone?
Digital certificates identify computers, phones and apps for security. Just like you'd use your driver's licence to show that you can legally drive, a digital certificate identifies your phone and confirms that it should be able to access something. Important: You're using an older Android version.
Why do we need certificates?
Websites need SSL certificates to keep user data secure, verify ownership of the website, prevent attackers from creating a fake version of the site, and convey trust to users.
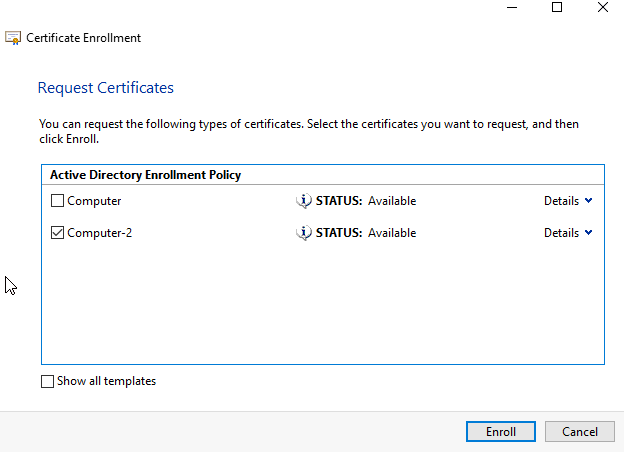
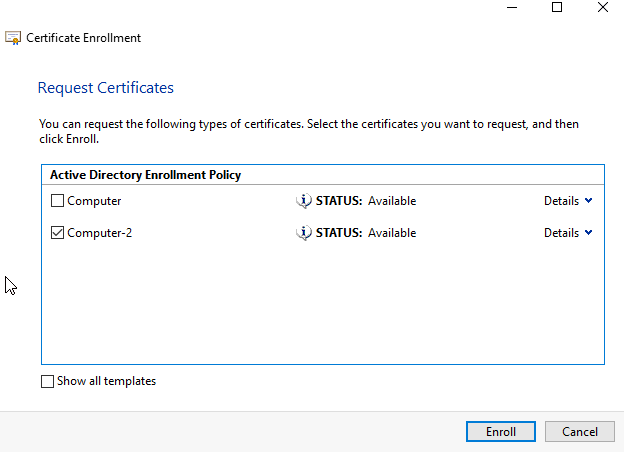
How do I create a device certificate?
Creating the Device Certificate (Certificate Issued by a Certificate Authority)Open a Web browser.Click [Login]. ... Click [Configuration], and then click [Device Certificate] under "Security" . ... Check the radio button next to the number of the certificate you want to request.Click [Request].Make the necessary settings.More items...
What are securities certificates?
Securities certificates are the written evidence of the ownership of shares of stock in, or an obligation to the bondholder by, a particular company.
How do websites get security certificates?
For an SSL certificate to be valid, domains need to obtain it from a certificate authority (CA). A CA is an outside organization, a trusted third party, that generates and gives out SSL certificates. The CA will also digitally sign the certificate with their own private key, allowing client devices to verify it.
What is the value of security certifications?
It shows that you have invested money, time and effort to acquire expertise in certain areas. As a professional, your certifications will help distinguish you from others on the job market. Credentials show that you have security knowledge and skills and therefore will add value to an organization or community.
What happens if I remove all certificates from my phone?
Removing all credentials will delete both the certificate you installed and those added by your device.
What is a device certificate?
A device certificate is a unique identifier used to authenticate phones and other devices. It's crucial for security against IP attacks. Learn more here. A device certificate is a unique, one-of-a-kind identifier used to authenticate a phone or other device.
Can a hacker intercept a password?
Ensure that the communication to your device is secure at both ends, and a hacker cannot intercept passwords or customer account identity information. Make activating your device easier with automated provisioning and simple activation.
What is the process of sending a certificate to a browser?
Before a browser and an HTTPS server can exchange data over an encrypted connection, they first engage in a process known as the SSL handshake. One important part in the SSL handshake is the sending of the server certificate to the web browser. It's here when the Web browser is able to authenticate the identity of the server it's connecting to.
How does a browser verify a certificate?
As soon as the browser receives a copy of the server certificate, it checks which CA signed the server cert and then retrieves the CA certificate of that particular Certificate Authority. It then uses the public key on that CA certificate to verify the digital signature on the server cert.
What happens after a digital signature is authenticated?
Once the digital signature has been authenticated, the browser and server can proceed with the rest of the SSL process. If you want to know how the public key on the server certificate is used, I suggest you read the article Roles of Server and Client Keys in Secure File Transfers.
What is CA certificate?
CA Certificates - the certificates in your browser. Before any major Web browser like Chrome, Firefox, Safari or Internet Explorer connects to your server via HTTPS, it already has in its possession a set of certificates that can be used to verify the digital signature that will be found on your server certificate.
Do CA certificates have public keys?
The private keys that are used for signing the server certificates already have their corresponding public key pairs on our users' Web browsers.
Why is the device CA certificate used in the IoT Edge security daemon?
Because the device CA certificate is used by the IoT Edge security daemon to generate the final IoT Edge certificates, it must itself be a signing certificate, meaning it has certificate signing capabilities. Applying "V3 Basic constraints CA:True" to the device CA certificate automatically sets up the required key usage properties.
Why is the edge CA certificate used?
Because the edge CA certificate is used by the IoT Edge security daemon to generate the final IoT Edge certificates, it must itself be a signing certificate, meaning it has certificate signing capabilities. Applying "V3 Basic constraints CA:True" to the edge CA certificate automatically sets up the required key usage properties.
What is an IoT edge certificate?
The IoT Edge hub server certificate is the actual certificate presented to leaf devices and modules for identity verification during establishment of the TLS connection required by IoT Edge. This certificate presents the full chain of signing certificates used to generate it up to the root CA certificate, which the leaf IoT device must trust. When generated by IoT Edge, the common name (CN), of this IoT Edge hub certificate is set to the 'hostname' property in the config file after conversion to lower case. This configuration is a common source of confusion with IoT Edge.
What is the purpose of a workload certificate?
The purpose of this "workload" intermediate certificate is to separate concerns between the device manufacturer and the device operator. Imagine a scenario where an IoT Edge device is sold or transferred from one customer to another. You would likely want the device CA certificate provided by the manufacturer to be immutable. However, the "workload" certificates specific to operation of the device should be wiped and recreated for the new deployment.
What is OpenSSL certificate path?
OpenSSL is used to connect to the IoT Edge hub, validate, and dump out the certificates.
How does a certificate chain of trust work?
The certificate chain of trust works by initially issuing a root certificate, which is the basis for trust in all certificates issued by the authority . Afterwards, the owner can use the root certificate to issue additional intermediate certificates ('leaf' certificates).
What is CA certificate?
The certificate authority, or 'CA' for short, is an entity that issues digital certificates. A certificate authority acts as a trusted third party between the owner and the receiver of the certificate. A digital certificate certifies the ownership of a public key by the receiver of the certificate.
How are certificates created?
Certificates are created in a hierarchy where each individual certificate is linked to the CA that issued the certificate. This link is to the CA’s certificate. The CA’s certificate then links to the CA that issued the original CA’s certificate. This process is repeated up until the Root CA’s certificate is reached. The Root CA’s certificate is inherently trusted.
What is digital certificate?
In brief, a digital certificate is a part of a public key infrastructure (PKI), which is a system of digital certificates, certificate authorities, and other registration authorities that verify and authenticate the validity of each party involved in an electronic transaction through the use of public key cryptography.
How to find out if a certificate has been revoked?
To find out which certificates are revoked, each issuer publishes a time- and date-stamped certificate revocation list ( CRL). The list can be checked using either online revocation or offline revocation by setting the RevocationMode or DefaultRevocationMode property of the following classes to one of the X509RevocationMode enumeration values: X509ClientCertificateAuthentication, X509PeerCertificateAuthentication, X509ServiceCertificateAuthentication, and the IssuedTokenServiceCredential classes. The default value for all properties is Online.
How to view a digital certificate chain?
You can view any certificate's chain using the MMC snap-in by double-clicking any certificate, then clicking the Certificate Path tab. For more information about importing certificate chains for a Certification authority, see How to: Specify the Certificate Authority Certificate Chain Used to Verify Signatures.
What is a personal certificate store?
This store is used for certificates associated with a user of a computer. Typically this store is used for certificates issued by one of the certification authority certificates found in the Trusted Root Certification Authorities store. Alternatively, a certificate found here may be self-issued and trusted by an application.
What is a certificate authority?
A certification authority issues certificates and each certificate has a set of fields that contain data, such as subject (the entity to which the certificate is issued), validity dates (when the certificate is valid), issuer (the entity that issued the certificate), and a public key. In WCF, each of these properties is processed as a Claim, ...
What is a public key?
The public key can be used to encrypt messages sent to the owner of the certificate. Only the owner has access to the private key, so only the owner can decrypt those messages. Certificates must be issued by a certification authority, which is often a third-party issuer of certificates.
