- Open the Command Prompt (cmd) as Administrator.
- Execute the command below to create a key pair: $ gpg –full-generate-key.
- Now, It prompts with the below configurations based on the information provided by the requestor: ...
- Export the Public and Private Keys:
How to Generate PGP Key Pair?
What is PGP cryptography?
How does PGP work?
What is PGP used for?
How does a session key work?
Where are public and private keys saved?
Can PGP be used for email verification?
See 4 more
About this website
How do I generate a public and private key in PGP?
Generate A Key PairOpen a command shell or DOS prompt.On the command line, enter: pgp --gen-key [user ID] --key-type [key type] --bits [bits #] --passphrase [passphrase] ... Press "Enter" when the command is complete. ... PGP Command line will now generate your keypair.
How do I create a public and private key for encryption?
How to Create a Public/Private Key PairStart the key generation program. ... Enter the path to the file that will hold the key. ... Enter a passphrase for using your key. ... Re-enter the passphrase to confirm it. ... Check the results. ... Copy the public key and append the key to the $HOME/.
How do I generate a PGP key in Windows?
Creating the keypairDownload the latest version of GPG4Win.Run the GPG4Win installer. ... Open Kleopatra.Go to File > New Key Pair.Select the option Create a personal OpenPGP key pair.Type a Name/Email address (at least one is required to continue) and click Next.Click Create.Enter a passphrase for the keypair and clock OK.More items...•
What is public and private PGP key?
PGP, Pretty Good Privacy, is a "public key cryptosystem." (Also known as PKC.) In PGP, each person has two "keys": a "public key" that you give to other people, and a "private key" that only you know. You use public keys to encrypt messages and files for others or to add users to PGP Virtual Disk volumes.
How do I create a new public key?
To generate an SSH private/public key pair for your use, you can use the ssh-keygen command-line utility. You can run the ssh-keygen command from the command line to generate an SSH private/public key pair. If you are using Windows, by default you may not have access to the ssh-keygen command.
How do I create a private key for my certificate?
ProcedureOpen the command line.Create a new private key in the PKCS#1 format. openssl genrsa -des3 -out key_name .key key_strength. For example: openssl genrsa -des3 -out private_key. ... Create a certificate signing request (CSR). The request is associated with your private key and is later transformed into a certificate.
How do I find my PGP key?
Open PGP Desktop.On the menu bar, click Tools and then Search for Keys. The Search for Keys window appears.Click the down arrow to the right of Search to select where to search for keys. To search the PGP Global Directory, select keyserver.pgp.com.
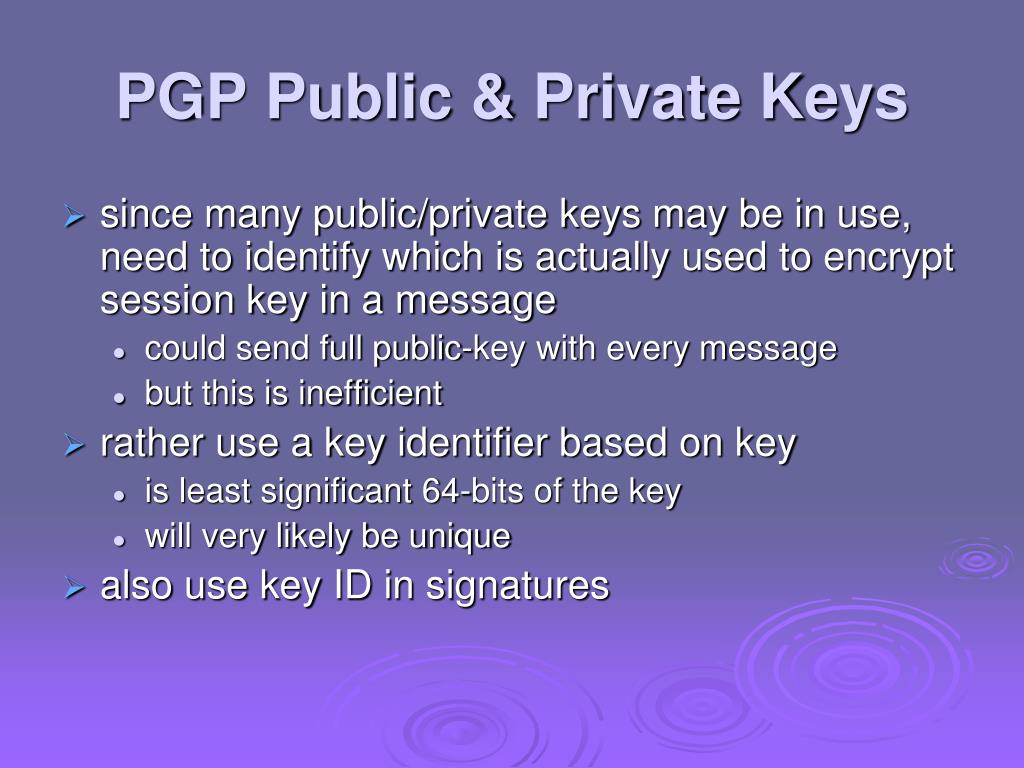
What is PGP key ID?
In PGP, most keys are created in such a way so that what is called the "key ID" is equal to the lower 32 or 64 bits respectively of a key fingerprint. PGP uses key IDs to refer to public keys for a variety of purposes.
What does PGP mean?
Pretty Good Privacy| Last updated April 6, 2020. Pretty Good Privacy (PGP) is an encryption system used for both sending encrypted emails and encrypting sensitive files. Since its invention back in 1991, PGP has become the de facto standard for email security.
How does private public key work?
Public key cryptography is a method of encrypting or signing data with two different keys and making one of the keys, the public key, available for anyone to use. The other key is known as the private key. Data encrypted with the public key can only be decrypted with the private key.
Is PGP still used today?
PGP encryption is most commonly used to secure email communications. But email security can be further enhanced by combining PGP encryption with PGP digital signature verification. It works as follows: Data from the sender's key is combined with the data being transferred.
How do I install PGP?
To install PGP Command Line onto a Windows system:Close all Windows applications.Download the zip file PGPCommandLine*. ... Unzip the file and the *. ... Open a command prompt as a local administrator.Install using msiexec. ... Follow the on-screen instructions.If prompted, restart your machine.
How do you generate a public and private key in RSA algorithm?
Generation of RSA Key PairGenerate the RSA modulus (n) Select two large primes, p and q. ... Find Derived Number (e) Number e must be greater than 1 and less than (p − 1)(q − 1). ... Form the public key. The pair of numbers (n, e) form the RSA public key and is made public. ... Generate the private key.
How do you make an AES?
On the command line, type:For 128-bit key: openssl enc -aes-128-cbc -k secret -P -md sha1.For 192-bit key: openssl enc -aes-192-cbc -k secret -P -md sha1.For 256-bit key: openssl enc -aes-256-cbc -k secret -P -md sha1. “secret” is a passphrase for generating the key. The output from the command is similar to:
Which encryption type uses a public and private key pair for encrypting and decrypting data?
Asymmetric encryptionAsymmetric encryption uses a mathematically related pair of keys for encryption and decryption: a public key and a private key. If the public key is used for encryption, then the related private key is used for decryption.
How do I create a public and private key in Linux?
Creating Private Key and Public Key (Linux)Open the terminal (e.g. xterm) on your client computer.Enter the following command in the terminal: ssh-keygen -t rsa. ... Enter the complete file path where the key pair is to be saved. ... Optional Enter a password and repeat it.
How to Create Keys for PGP - Stack Abuse
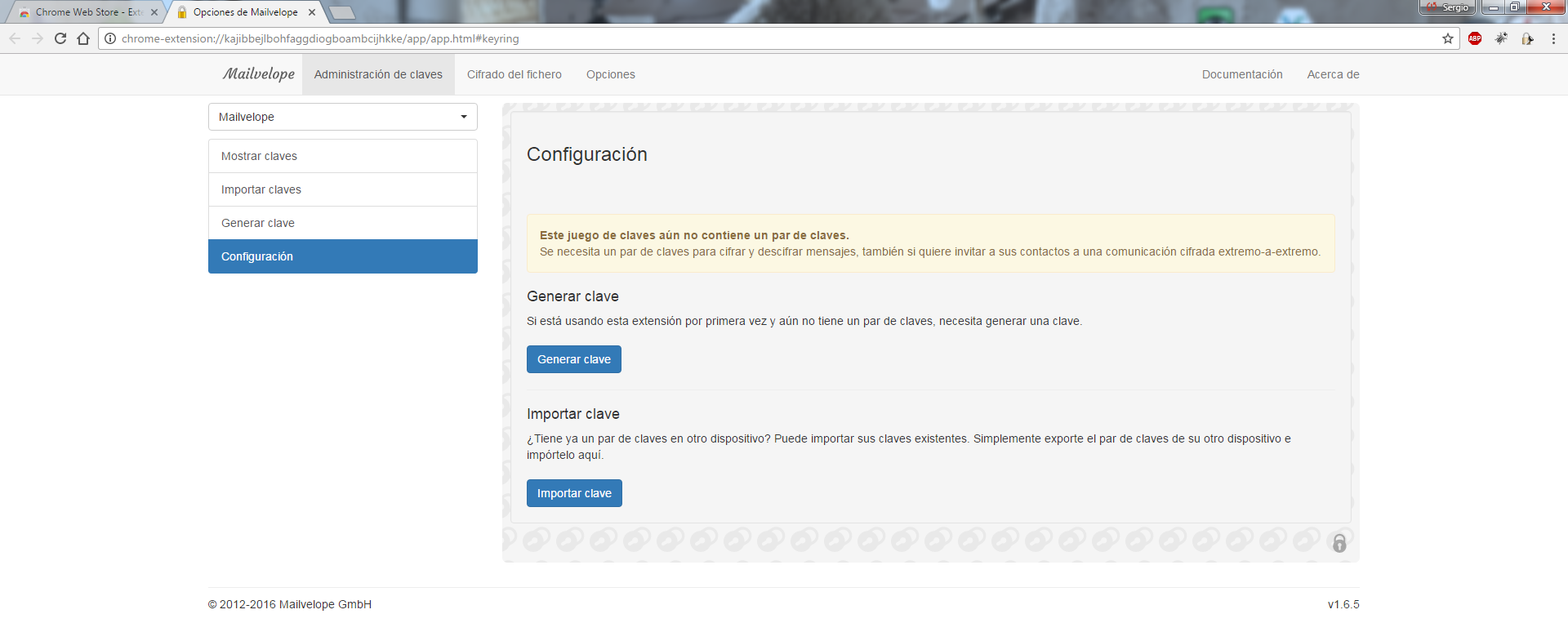
As simple as the concept of encryption sounds - "use a key to encrypt your data" - its not always straightforward to do. Here, we explain the first step, creating your encryption keys. This how-to describes the method of creating keys for PGP using GnuPG , the GNU project's complete and free implementation of the OpenPGP standard as defined by RFC4880 .
How to generate PGP keys with GPG - Linux Hint
PGP is mostly used for encrypting and decrypting documents, texts, and emails in order to improve security of the communication. It uses the public key of the sender for encrypting the message and then decrypts it with the private key of the intended user. This article explained the method of generating PGP keys with the help of --gen-key, --full-gen-key, and the --quick-gen-key GPG options.
How to create a private and public key pair with PUTTYGEN
This guide describes how to generate and use a private/public key pair to log in to a remote system with SSH using PuTTY. Using key-based SSH logins, you can disable the normal username/password login procedure which means that only people with a valid private/public key pair can log in. That way, there is no way for brute-force attacks to be successful, so your system is more secure.
PGP Key Generator | Gravity Forms PGP Encryption plugin by wp2pgpmail
Concerning the PGP Key Generator, we DO NOT record any data: no e-mail address, no password and no messages. If you wish to place an order, your details will be requested. Some services require the use of cookies to work, and these cookies can not be disabled: - The very site of wp2pgpmail, if you identify yourself by logging into your account;
HOW TO: Create a PGP Key in Encryption Desktop for Windows - Support Portal
This article details how to create a PGP key using Symantec Encryption Desktop (previously PGP Desktop) for Windows. PGP Keys are essential to the use of Encryption Desktop, it is important to backup your keys by either exporting the key(s) them to a file and storing in a secure location, or by using the backup feature provide within Encryption Desktop (see the Backup option within PGP Options).
How to Generate PGP Key Pair?
It encrypts data and provides cryptographic privacy and authentication for online communication. It is frequently used to encrypt documents, emails, and files to improve email security. Data compression, hashing, and public-key cryptography are all used in PGP encryption. PGP also verifies the sender’s identity and ensures that the message was not tampered with while in transit.
What is PGP cryptography?
PGP is a type of hybrid cryptography. PGP combines the best features of both symmetric and public-key cryptography in one bundle. When a user encrypts plaintext with PGP, the plaintext is compressed first. Data compression reduces transmission time and disc space use while also improving cryptographic security. Most cryptanalysis techniques use patterns present in plaintext to exploit the cipher. Compression increases cryptanalysis resistance by reducing the patterns in plaintext (Files with very small sizes are not compressed).
How does PGP work?
PGP generates a session key, which is a secret key and is generated only once. This key generates a random number from the movement of your cursor and the keystrokes you type. This session key is used to encrypt the plaintext with a very secure and fast symmetric encryption algorithm, and the output is ciphertext. The session key is then encrypted with the recipient’s public key after the data has been encrypted.
What is PGP used for?
To verify the sender’s identity. Encrypt Data: PGP can be used to encrypt files. PGP offers a highly secure solution of encrypting data at rest, especially when combined with a Threat Detection and Response Solution. The algorithm used by PGP – typically the RSA algorithm – is nearly unbreakable.
How does a session key work?
The session key is then encrypted with the recipient’s public key after the data has been encrypted. The decryption of encrypted data works in reverse. The temporary session key can be recovered using the recipient’s private key, which is then used to decrypt the ciphertext encrypted with symmetric cryptography.
Where are public and private keys saved?
Note: Both Public and Private keys will be saved in the directory where the export commands are executed.
Can PGP be used for email verification?
As more individuals become aware of how much data corporations and governments collect, many people are now using the standard to keep their personal information private. Identity Verification: PGP can also be used for email verification.
How to access public key?
To access your public key (the one you will be posting into your account or sharing with others), right-click the field with the key pair name and press “Details” at the bottom of the menu. 9. Next, press the “Export” button. This will bring up the contents of your public key. 10.
How to sign text using PGP key?
In order to sign text using your PGP private key, simply copy and paste the text you wish to sign into your clipboard. Then, under the. Tools.
What is PGP in darknet?
PGP stands for “Pretty Good Protection” and is a method of encrypting and verifying digital information such as emails, text messages, and other documents. For instance, most darknet markets require that their members provide a PGP public key upon registration of their account in the case that sensitive messages need to be sent from one member to another. The signing of such a message involves the sender using the public key of the recipient to encrypt the message. The recipient then uses their private key to decrypt the message.
How to copy and paste PGP?
This is your PGP public key, and what you will be pasting for online verification purposes. Paste (ctrl+v) it into a text document and save it in a place where you will remember where it is.
How many keys are generated during PGP?
The recipient then uses their private key to decrypt the message. Thus, there are 2 keys generated during the PGP key creation process: public and private.
What is a public key?
The public key is the one you will want to share with others (thus the name “public key”). There are several different ways to generate PGP key pairs; in this article we will be using a program called Gpg4win, also known as Kleopatra.
How long are key pairs valid?
Note that a key pair is only valid for 2 years under the default option. You can increase or decrease the length of time for which your keys are valid by clicking on the “Advanced Settings” button and adjusting the. Valid until. field (uncheck the box next to the field if you want your keys to never expire).
How to export a Kleopatra key?
1. Open Kleopatra#N#2. Right click on the new keypair that was created earlier#N#3. Click Export Secret Keys#N#4. Save the file locally, adding the extension manually to the filename#N#NOTE: DO NOT save the key as "ASC". EV.c only accepts .PGP, .cert, or .crt extensions#N#5. Login to Manage console with an administrator account#N#6. Go to Archive Collectors > Bloomberg > Bloomberg Settings#N#7. Enter in the following and click Save:#N#- Firm Code#N#- FTP Login#N#- FTP Password#N#8. On the Upload Encryption Key section, click Browse and Upload. Navigate to the private key that was exported in step 4#N#9. Enter the passphrase that was set during the keypair creation#N#10. Click Upload
How to open a Kleopatra file?
1. Open Kleopatra#N#2. Right-click on the new keypair that was created earlier#N#3. Click Export#N#4. Save the file locally#N# 5. Login to Bloombergs CCNS<GO>#N#6. Go to the Public Keys tab#N#7. Click Add#N#8. From the Key Type: drop-down, select Encryption#N#9. Open the public key, that was exported in step 4, in any text editor ( ie: notepad)#N#10. Copy all of the contents of the public key and paste them into CCNS<GO>#N#NOTE: Be sure to include the "-----BEGIN PGP PUBLIC KEY BLOCK-----" and "-----END PGP PUBLIC KEY BLOCK-----" in the copied/pasted text#N#11. Click Add#N#12. Click Submit
How to install Kleopatra on Windows 10?
1. Download the latest version of GPG4Win#N#2. Run the GPG4Win installer. This will install Kleopatra and add new options to the Windows Right-Click menu#N#3. Open Kleopatra#N#4. Go to File > New Key Pair#N#5. Select the option Create a personal OpenPGP key pair#N#6. Type a Name/Email address (at least one is required to continue) and click Next#N#7. Click Create#N#8. Enter a passphrase for the keypair and clock OK#N#NOTE: Be sure to write down/remember this passphrase is it will be needed later#N#9. Click Make a backup of your keypair and save a local copy of the keypair for backup purposes#N#10. Enter the passphrase for the keypair and click Ok#N#11. Click Finish
What is the key ID for PGP?
PGP Command line will now generate your keypair. You should see your Key ID (i.e. 0X12345678) , and a message that the key was successfully generated.
How to import a public key?
You may import a public key from an ASCII Armor file (.asc) or from a text file, the process is the same for both. The file containing the key (s) to be imported must be in the current directory. As with exporting a key, this will be referred to as (input) in the examples. Both public and private keys will be imported if they exist in the file. If a key being imported already exists in the local keyring, the keys are merged. Import Key From File: 1 Open a command prompt. 2 From the command prompt, enter:#N#pgp --import (input) 3 Press "Enter" when the command is complete.
How does PGP respond to commands?
PGP Command Line responds by exporting keys as ASCII armor (.asc) files into the directory currently active on the command line . Example 1 The following example will show you how to export your public key using your key ID.
Can I import a public key from an ASCII file?
You may import a public key from an ASCII Armor file (.asc) or from a text file , the process is the same for both. The file containing the key (s) to be imported must be in the current directory. As with exporting a key, this will be referred to as (input) in the examples. Both public and private keys will be imported if they exist in the file. If a key being imported already exists in the local keyring, the keys are merged. Import Key From File:
What is public PGP?
Typically you import the public keys of several other users into your keyring, and export your own public key to send to other users. There is usually little security risk associated with distributing your public key. Public PGP keys are those for which you lack a private key. Private/public keypairs (also known as secret keys or private keys) ...
Why are private key pairs listed as private in Moveit?
In MOVEit Automation Admin, private/public keypairs are listed as Private because you have the private keys.
How many keys are in a company's key pair?
This is your key pair (or your company's). It consists of one private key and one public key.
Can you export a public key?
Typically you import the public keys of several other users into your keyring, and export your own public key to send to other users. There is usually little security risk associated with distributing your public key.
Do you need a password for a private key pair?
Although a password is not required, private/public keypairs are typically encrypted with a password.
Prerequisites
First we need to download PuTTYgen on our Windows system. PUTTYgen only usage is to create the private/public key pair, we then need Putty to connect to the VPS. Both PUTTYgen and Putty can be downloaded from this page here.
Create the key pair
We will use PuTTYgen to create a private/public key pair. When started, find Type of key to generate and select SSH-2 RSA and then set Number of bits in a generated key to 1024.
Save the public key
Then click on Save public key and save it in some safe location on your computer. You are free to choose a filename and extension, but it should be one that lets you remember for which system it is.
Save the private key
Before we save the private key we should enter a Key passphrase and repeat it under Confirm passphrase . The passphrase will be used to encrypt the key on disk, without the passphrase you will not be able to use the key and it would be of no use. If you leave the passphrase fields blank, the key will be saved unencrypted.
Add the public key to your server
Select All text in the textbox Public key for pasting into OpenSSH authorized_keys file, right-click and copy the public key from the PuTTYgen window:
Tell Putty to use the private key when connecting to your server
Start Putty and from the Category window, select Connection | SSH | Auth and click the Browse… button.
What does Bob see when he downloads Alice's public key?
Bob sees the message from Alice, but wants to confirm it's really from her. He downloads Alice's public key and verifi es that the message corresponds to her public key.
Can you unlock a padlock with a key?
Let say you have a padlock and its key to unlock the padlock. And you distributed the padlocks to someone who wants to send you the messages. When someone wants to send the message, he will lock the message with the padlock that you shared. After locking the message with your padlock, you are the only one who can unlock it because you have a unique key to open the padlock.
How to Generate PGP Key Pair?
It encrypts data and provides cryptographic privacy and authentication for online communication. It is frequently used to encrypt documents, emails, and files to improve email security. Data compression, hashing, and public-key cryptography are all used in PGP encryption. PGP also verifies the sender’s identity and ensures that the message was not tampered with while in transit.
What is PGP cryptography?
PGP is a type of hybrid cryptography. PGP combines the best features of both symmetric and public-key cryptography in one bundle. When a user encrypts plaintext with PGP, the plaintext is compressed first. Data compression reduces transmission time and disc space use while also improving cryptographic security. Most cryptanalysis techniques use patterns present in plaintext to exploit the cipher. Compression increases cryptanalysis resistance by reducing the patterns in plaintext (Files with very small sizes are not compressed).
How does PGP work?
PGP generates a session key, which is a secret key and is generated only once. This key generates a random number from the movement of your cursor and the keystrokes you type. This session key is used to encrypt the plaintext with a very secure and fast symmetric encryption algorithm, and the output is ciphertext. The session key is then encrypted with the recipient’s public key after the data has been encrypted.
What is PGP used for?
To verify the sender’s identity. Encrypt Data: PGP can be used to encrypt files. PGP offers a highly secure solution of encrypting data at rest, especially when combined with a Threat Detection and Response Solution. The algorithm used by PGP – typically the RSA algorithm – is nearly unbreakable.
How does a session key work?
The session key is then encrypted with the recipient’s public key after the data has been encrypted. The decryption of encrypted data works in reverse. The temporary session key can be recovered using the recipient’s private key, which is then used to decrypt the ciphertext encrypted with symmetric cryptography.
Where are public and private keys saved?
Note: Both Public and Private keys will be saved in the directory where the export commands are executed.
Can PGP be used for email verification?
As more individuals become aware of how much data corporations and governments collect, many people are now using the standard to keep their personal information private. Identity Verification: PGP can also be used for email verification.
