
See more
Is AWS safe and secure?
Benefits of AWS security Keep Your data safe — The AWS infrastructure puts strong safeguards in place to help protect your privacy. All data is stored in highly secure AWS data centers. Meet compliance requirements — AWS manages dozens of compliance programs in its infrastructure.
Is AWS a secure platform?
AWS provides services that help you protect your data, accounts, and workloads from unauthorized access. AWS data protection services provide encryption and key management and threat detection that continuously monitors and protects your accounts and workloads.
Can AWS be hacked?
Ec2 instances run at the heart of AWS and they are essentially virtual machines. With this compute power hackers can exploit your account to mine things such as cryptocurrency.
What are the risks of AWS?
Top AWS Cloud Security RisksPoor Identity and Access Management. ... Understanding Liability. ... Improper Data Encryption. ... Non- Compliance. ... AMIs Made Public. ... AWS Identity And Access Management. ... AWS Macie. ... AWS Artifact.More items...•
Which is more secure AWS or Azure?
AWS and Azure are almost evenly matched. Except AWS offers slightly more secure encryption with the addition of the Galois Counter Mode (GCM). Furthermore, AWS has more encryption services and key management options. Finally, AWS has more in-depth documentation for its services and options than Azure.
Which cloud platform is most secure?
The following are the list of most secure cloud storage of 2021:IDrive.pCloud.Sync.com.Microsoft OneDrive.Google Drive.Egnyte Connect.MEGA.Tresorit.More items...•
Does the FBI use AWS?
Similarly, the Federal Bureau of Investigation (FBI) has also made significant use of AWS for its investigative efforts. However, it should be noted that the DoD and FBI are not the only government agencies that have made significant use of AWS.
When was the last time AWS was hacked?
In 2015, a hacker gained access to an AWS server and was able to view customer data. In 2016, another hacker was able to gain access to an AWS S3 bucket and view customer data. In February 2018, AWS was hit with a massive cyberattack that impacted dozens of companies, including Amazon.
Can Amazon steal data from AWS?
“If you have a single shared computer running your cloud and running your customer code, one customer can see the other customer's data, Amazon can see your data, and the customers can change the Amazon code and hack the system and take control of the code and steal data.”
What is the disadvantage of using AWS?
Disadvantages of AWS Amazon Web Services may have some common cloud computing issues when you move to a cloud. For example, downtime, limited control, and backup protection. AWS sets default limits on resources which vary from region to region. These resources consist of images, volumes, and snapshots.
What is AWS biggest challenge?
Migration of Legacy system Migration of these systems to AWS is the biggest challenge. The businesses have to define the immediate and long-lasting solutions. In such cases, hybrid cloud is essential where the legacy system and cloud applications are used.
Why is azure better than AWS?
Due to its almost 7-year operating history, AWS has greater resources, infrastructure, and superior, scalable services than Azure. More significantly, while Azure was attempting to catch up, Amazon could expand its cloud infrastructure by adding more servers and utilizing economies of scale more effectively.
Is AWS good for cybersecurity?
AWS provides cybersecurity services that help you to: Protect your data, accounts, and workloads from unauthorized access. Manage identities, resources, and permissions at scale. Enforce fine-grained security policy at network control points across your organization.
How safe is my data on AWS?
AWS has achieved internationally recognized certifications and accreditations for compliance with privacy assurance frameworks, such as ISO 27017 for cloud security, ISO 27701 for privacy information management, and ISO 27018 for cloud privacy.
Does the FBI use AWS?
Similarly, the Federal Bureau of Investigation (FBI) has also made significant use of AWS for its investigative efforts. However, it should be noted that the DoD and FBI are not the only government agencies that have made significant use of AWS.
Can I use AWS as a VPN?
AWS VPN offers two valuable services: AWS Site-to-Site VPN and AWS client VPN. AWS Site-to-Site VPN enables you to securely connect your on-premises network or branch office site to your Amazon Virtual Private Cloud (Amazon VPC). AWS Client VPN allows you to securely connect users to AWS or on-premises networks.
What is the biggest worry about AWS?
The security of the cloud, a.k.a. the security of the physical and staff resources of AWS, is usually the biggest worry. Here are some resources to help you gauge AWS’ commitment to security:
What tools can be used to protect AWS?
Many of the tools you already use to protect your environment — like WAFs, network setup, central authentication, etc. — can be applied to AWS
Why was AWS created?
Not incidentally, these cloud automation features are why AWS was created in the first place. Amazon did not just require endless compute power , they wanted a layer of abstraction between their developers and their systems that enabled them to test and ship new features more quickly. Underneath the covers, automation and templatization are what has allowed Amazon to become the eCommerce giant they are today.
What is cloud security?
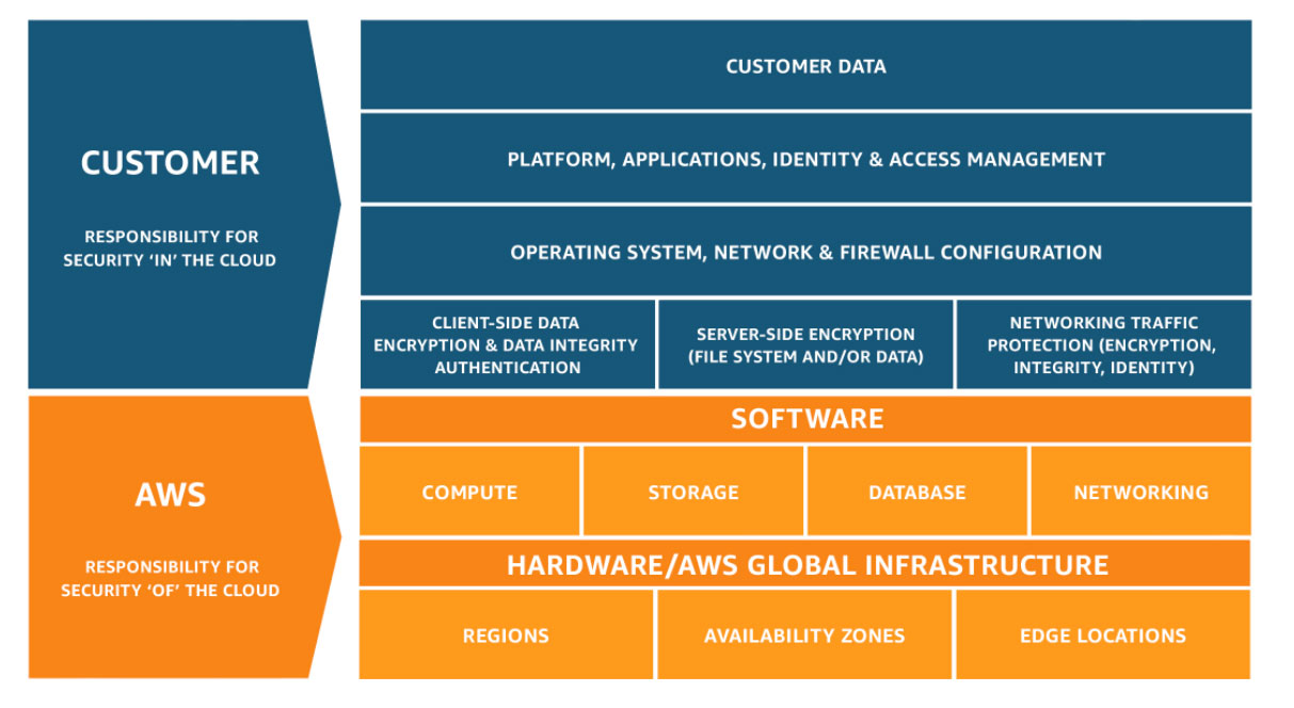
Security in the cloud refers to the security of systems built on top of AWS. While AWS provides a simplified system for administrators to both implement and audit standard security measures, it by no means replaces these traditional measures nor promises the security of your systems. Just as in a traditional data center or private cloud, the security of your system is your responsibility.
Does AWS require PCI?
Every retailer that processes credit card payments must be PCI certified. AWS’ certification provides an immediate benefit to retailers by taking care of the compliance of the infrastructure, but retailers must prove that people and processes are also compliant. Numerous organizations have received PCI certification on the AWS platform, and many claim that certification is significantly less costly and time-consuming on AWS than in their own datacenter.
Is AWS more secure than GE?
Whenever a CIO or CTO claims that AWS is more secure than their datacenter, as GE did last year, what they usually mean is that the security tools that AWS provides enable greater transparency and reinforcement of traditional security measures.
Is AWS security in the cloud?
Security in the cloud has many of the same features of network and application-level security in a traditional environment, though many organizations enlist outside help in translating traditional protections to AWS.
How to secure AWS?
With the help of a cloud security solution, businesses can easily manage their responsibilities for securing their sensitive data and applications in the cloud. Here are some best practices to help you choose the right solution: 1 Easy integration. Choose a security solution that integrates with AWS to make the process painless. 2 Maintain visibility and control. To be able to effectively audit and control compliance, choose a solution that allows total visibility and control. Ideally, a security solution will provide the visibility necessary for identifying sensitive data in the cloud and then implement automated, immediate responses to keep your organization in compliance. 3 Context, system, and user awareness. A security solution should be context-, system-, and user-aware to more effectively identify and block suspicious behavior and protect your data without interrupting the flow of operations. 4 Automatic response to user activity. Choose a cloud security solution that automatically prompts or blocks user activity based on context, logs the event, and audits the activity for forensic analysis. 5 Detailed logging and reporting. A good cloud security solution offers detailed logging and reporting for analysis, allowing you to identify patterns and trends and adjust data protection programs accordingly. 6 Unified cloud and on-premise security. Some solutions work in tandem with on-premise data protection solutions, allowing for more comprehensive security and consistent policies. By simplifying policy management, you will cut down on costs and eliminate policy gaps that can lead to vulnerabilities.
What is AWS network?
Unlike your on-site systems, which have a hierarchical structure and a peripheral network that scrubs and analyzes data being transmitted, AWS makes it possible for every instance to communicate with the Internet. The exposed applications structure requires you to strengthen existing security controls.
What is AWS audit?
AWS offers a robust suite of Compliance Resources, including an auditing security checklist which helps businesses perform self-audits to ensure that regulatory requirements are met.
What is cloud HSM?
CloudHSM helps you generate encryption keys using managed hardware security modules, or HSMs, stored on your AWS deployments. CloudFront is Amazon’s content delivery network. It protects your applications from DDoS attacks and allows you to transfer data securely at high speeds.
What is AWS WAF?
AWS WAF (Web Application Firewall) allows you to create custom rules to keep your agile developments secure from common attacks such as SQL injections and XSS.
What is Amazon Web Services?
Amazon Web Services (AWS) is the leading provider of on-demand cloud services with more than a million customers. When the cloud was still new, the perceived lack of security hindered people from adopting it. While cloud security has come a long way, there are still many risks associated with it. Following recommended best practices can help ...
What is Amazon Cognito?
Amazon Cognito is used for identity management. It can detect brute force authentication, as well as fraudulent login attempts. Amazon Cognito works with third party services such as Microsoft Active Directory, Google and Facebook, allowing you to specify additional validation methods.