What is the primary purpose of penetration testing quizlet?
What is the primary purpose of penetration testing? Test the effectiveness of your security perimeter.
What is the purpose of penetration testing Mcq?
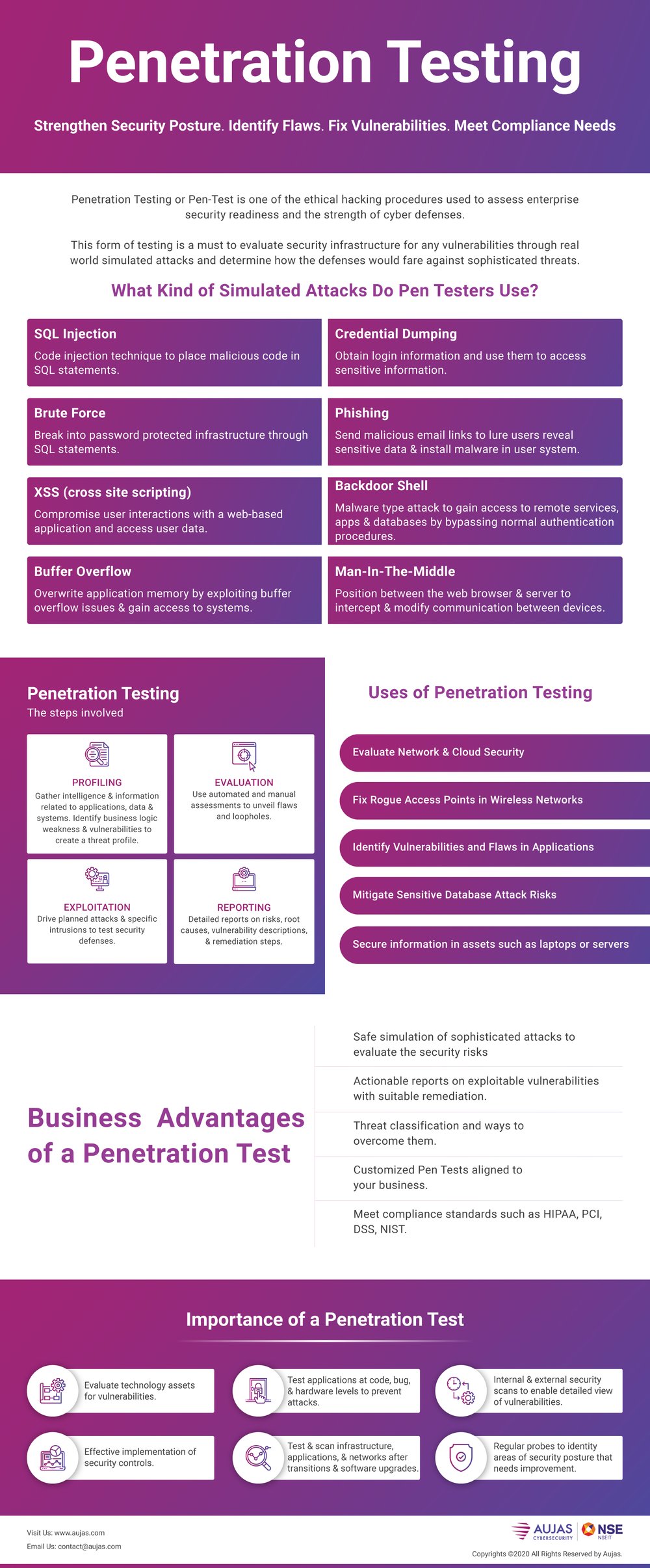
Penetration testing is evaluating the security of a computer system or network by simulating attacks on them.
Which of the following can be used for penetration testing?
Top Penetration Testing Software & ToolsNetsparker. Netsparker Security Scanner is a popular automatic web application for penetration testing. ... Wireshark. Once known as Ethereal 0.2. ... Metasploit. ... BeEF. ... John The Ripper Password Cracker. ... Aircrack. ... Acunetix Scanner. ... Burp Suite Pen Tester.More items...•
What is penetration testing and its types?
The different types of penetration tests include network services, applications, client side, wireless, social engineering, and physical. A penetration test may be performed externally or internally to simulate different attack vectors.
Which of the following is not included in penetration tests Mcq?
Which of the following is not included in penetration tests? Explanation: Penetration test does not identify the automated system failure. 3.
Which of the following is a correct statement in regard to penetration testing?
All of the above is the correct answer to the given question. Explanation: The Penetration testing is the method of evaluating the computer program, system as well as the web service to detect the bugs that could be performed the malicious activity.
Which tool is used for wireless penetration testing Mcq?
Clarification: WebInspect is a popular web application security tool used for identifying known vulnerabilities residing in web-application layer. It also helps in penetration testing of web servers.
What are the main penetration testing phases?
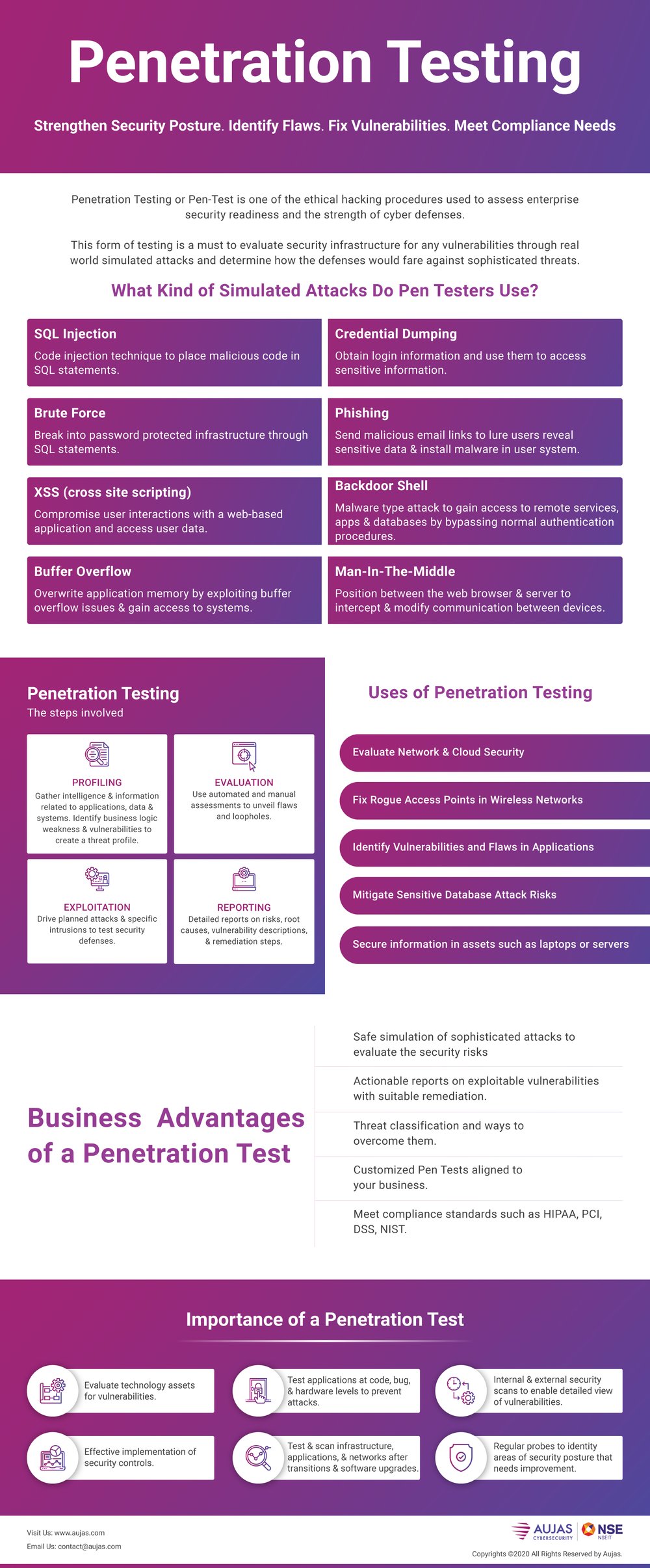
The Five Phases of Penetration TestingReconnaissance. The first phase of penetration testing is reconnaissance. ... Scanning. Once all the relevant data has been gathered in the reconnaissance phase, it's time to move on to scanning. ... Vulnerability Assessment. ... Exploitation. ... Reporting.
What is a pen test?
A penetration testing, or pen test, is an attempt to evaluate the security of an IT infrastructure by safely trying to exploit vulnerabilities. These vulnerabilities may exist in operating systems, services and application flaws, improper configurations, or risky end-user behavior. Such assessments are also useful in validating the efficacy of defensive mechanisms, as well as end-user adherence to security policies.
What is a rhynoehs pen test?
RhynoEHS delivers a web pen-testing service that is faster and more cost-efficient than others.
What is the purpose of penetration testing?
Another common question regarding what is the primary purpose of Penetration Testing is whether or not it is necessary to perform this type of testing if you are developing a software product. The truth is that performing an automated web vulnerability assessment is often a good idea regardless of whether or not you intend to sell a Web application. Automated vulnerability detection will help you develop a thorough security program by pinpointing specific security issues in your product. However, in some cases you may still need to engage in manual testing in order to discover the primary purpose of Web testing.
Why is penetration testing important?
While there is no way to avoid these threats completely, reducing the threat footprint of your business will go a long way towards protecting your sensitive data. This is why penetration testing is important. Pen Testing will let you determine whether or not a particular Web application is suitable for your organization, and whether or not it is protecting your data appropriate ly.
Why do businesses use penetration testing?
A Penetration Test is typically conducted in order to detect weak areas in a Web application and determine whether or not they present a risk to the security of your company.
What is penetration test?
A Penetration Test is conducted to verify the usability and security of a Web application. The objectives of this type of test are to detect any vulnerabilities in the application, as well as any areas of concern that could result in user or system compromise. Users may not be aware of all the potential threats they may face in the online environment. Through this process, weaknesses and vulnerabilities are identified that could potentially allow hackers and other bad elements to gain unauthorized access to a company’s data or systems.
Why do we do web vulnerability assessments?
The primary purpose of the primary goal of a Web vulnerability assessment is to identify security weaknesses on the client side. Common issues that are typically addressed during these assessments include memory holes, cross-site scripting vulnerabilities, SQL injection vulnerabilities, and application security issues. It is very common for companies to use client side testing as a way of discovering the most severe of security flaws. However, using client side testing is not enough to isolate the flaws that may exist in your Web application. For these reasons, comprehensive and effective testing is necessary to confirm the existence and severity of Web vulnerabilities.
What are the threats attacking my business?
Script Kiddie: A script kiddie is a loose term that relates to a summer student that, in an effort to learn about technologies, may find themselves exploiting and obtaining unauthorized access to various environments. While their underlying motivation may not be malice, they break various laws.
What motivates a hacker to compromise my website?
Understanding the various threats, the motivation to compromise your website depends heavily on the attacker. Targets of opportunity, who do not patch or adopt secure configuration standards, are a target for lower skilled attackers who may compromise your website just because they can.
Why do I need a penetration test?
If you store, process, or transmit Credit-cards, the PCI council may mandate that you do so. If not, there are various regulatory requirements most countries that mandate protection of privacy-related information (PII) via the PIPEDA law in Canada, personal health information (PHI) via the PHIPA law in Canada.
Why is penetration testing important?
A penetration testing process will enable your business to test where new vulnerabilities occur as your business grows and evolves.
What is penetration testing?
Penetration testing is a method of simulating a cyberattack to identify weaknesses in your computer system, network or web applications. It’s known as an ethical hack, as it’s used to improve your cybersecurity.
What is a pen test?
A pen test enables companies to see where their vulnerabilities occur and how these weaknesses can be exploited – whether this be through exposing sensitive information , the network or your applications. This test is carried out in a safe environment where the pen tester is working with your company rather than having malicious motivations. It’s a bit like carrying a test of your business continuity plan – you think you have everything in place but even the best plan can be shown to have a gaping hole when a question or challenge that no one has ever considered before, is asked.
Why do companies use pen tests?
Pen tests enable your company to see how your IT team reacts to an attack and their capabilities before a true hacker attacks your system. Identifying skillset gaps in a simulated cyberattack enables your cybersecurity to seek additional training and learn.
What industries require pen testing?
Many industries include penetration testing as part of their compliance legislation, such as healthcare, banking and service providers . Some common regulations that require pen tests to be compliant include
Who should approve cyber security tests?
There are overwhelming benefits in performing regular tests of your cyber defences, but this is task for a professional! Tests should be planned and approved by a senior leader in your organisation who should have board responsibility for your data security.
Are penetration tests worth it for SMEs?
In short, yes! All businesses should be organising pen tests and SMEs are no exception.
What is the difference between penetration testing and vulnerability scanning?
- Vulnerability scanning is performed with a detailed knowledge of the system; penetration testing starts with no knowledge of the system.
What is double blind test?
Double-blind test. - The tester does not have prior information about the system, and the administrator has no knowledge that the test is being performed. Match each network enumeration technique on the left with its corresponding description on the right. Drag.
What is penetration testing?
Penetration testing is the method to evaluate the security of an application or network by safely exploiting any security vulnerabilities present in the system. These security flaws can be present in various areas such as system configuration settings, login methods, and even end-users risky behaviors. Pentesting is required, apart from assessing security, to also evaluate the efficiency of defensive systems and security strategies.
What are the different approaches to Penetration Testing?
There are three approaches adopted by testers in regards to penetration testing, based on the information available and the type of weakness to be found:
How does Penetration Testing differ from Vulnerability Assessment?
The term Penetration Testing appears in the latter half of the term VAPT, which stands for Vulnerability Assessment and Penetration Testing. Quite understandably, people confuse VA (Vulnerability Assessment) & PT (Penetration Testing) as the same process and use them interchangeably. Well, they are not and shouldn’t be swapped with one another. The difference between them is crucial when judging how it fits the requirements. Both are essential security evaluators that help in strengthening your application’s security posture.
What is the difference between pentesting and vulnerability scan?
Cost is another factor that differentiates these two. Compared to pentesting, vulnerability assessments cost less. Vulnerability scan reports mainly contain a list of security vulnerabilities and a detailed description of these. While pentesting reports generally contain the vulnerabilities ranked according to their severity. ease of exploitation, and the extent of risk.
What is a pentest?
Pentests are usually comprised of both manual or automated tests, which aim to breach the security of the application with proper authorization. Once the vulnerabilities are discovered and exploited, the client is provided with a detailed penetration testing report containing information about the scope of the test, vulnerabilities found, their severity, and suggestions to patch them up.
What is vulnerability assessment?
Vulnerability assessments are mainly done by qualified technicians using automated tools, results of which are then compiled and attested. In comparison, pentesting is generally done by white hat hackers or ethical hackers. They are security experts and bring in the human element to break into a system. In pentesting, vulnerability assessment can be used in the initial steps to identify targets and potential attack vectors.
What to discuss before a security test?
Before even planning a test, it’s imperative that you along with your security provider discuss topics such as the scope of the test, budget, objectives, etc. Without these, there won’t be clear enough direction of the test and will result in a lot of wasted effort