What are windows logs used for?
Windows Logging Basics. Logs are records of events that happen in your computer, either by a person or by a running process. They help you track what happened and troubleshoot problems. The Windows event log contains logs from the operating system and applications such as SQL Server or Internet Information Services (IIS).
What is the windows sign-in process?
This process performs a variety of critical tasks related to the Windows sign-in process. For example, when you sign in, the winlogon.exe process is responsible for loading your user profile into the registry. This allows programs to use the keys under HKEY_CURRENT_USER, which are different for each Windows user account.
How do I view the Windows Event Log?
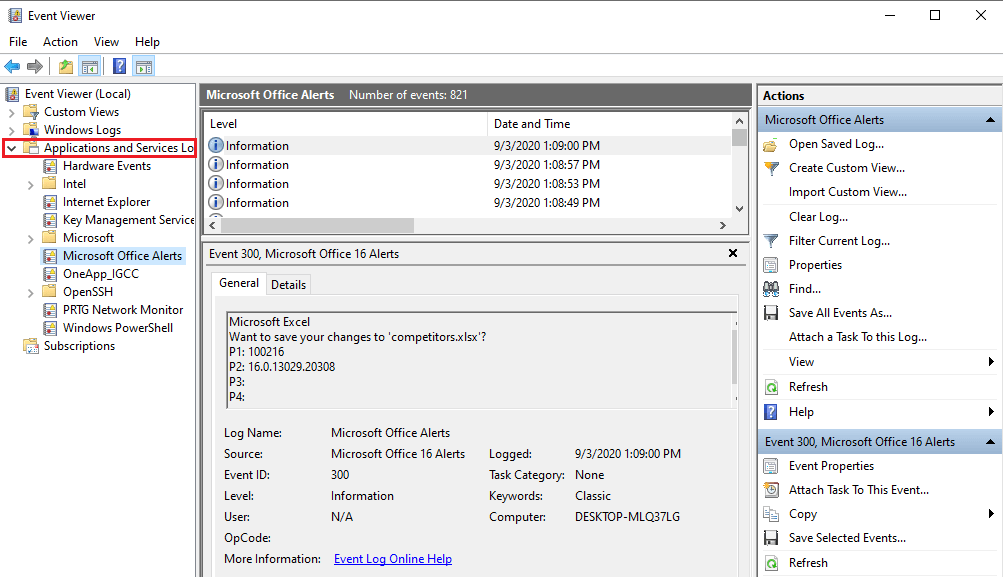
The Navigation pane is where you choose the event log to view. By default, there are five categories of Windows logs: Application – Information logged by applications hosted on the local machine. Security – Information related to login attempts (success and failure), elevated privileges, and other audited events.
Where are logs stored in Windows 10?
The most common location for logs in Windows is the Windows Event Log. It contains logs from the operating system and several applications such as SQL Server or Internet Information Server (IIS). The logs use a structured data format, making them easy to search for and analyze.
What is a secret key?
What is network logon?
What is RDP in remote desktop?
What is domain user account?
What is a SAM?
What is a domain credential?
What is interactive logon?
See 2 more
About this website

What is the logon process?
In general computer usage, logon is the procedure used to get access to an operating system or application, usually in a remote computer. Almost always a logon requires that the user have (1) a user ID and (2) a password.
What happens during Windows logon?
A local logon grants a user permission to access resources on the local computer or resources on networked computers. If the computer is joined to a domain, then the Winlogon functionality attempts to log on to that domain. A domain logon grants a user permission to access local and domain resources.
What is a window logon?
In computing, Winlogon (Windows Logon) is the component of Microsoft Windows operating systems that is responsible for handling the secure attention sequence, loading the user profile on logon, and optionally locking the computer when a screensaver is running (requiring another authentication step).
Which of the following Windows system processes are involved in authentication?
The Windows operating system implements a default set of authentication protocols, including Kerberos, NTLM, Transport Layer Security/Secure Sockets Layer (TLS/SSL), and Digest, as part of an extensible architecture.
How does Windows domain authentication work?
Here's how the authentication process goes: The client requests an authentication ticket from the AD server. The AD server returns the ticket to the client. The client sends this ticket to the Endpoint Server. The Server then returns an acknowledgment of authentication to the client.
What is interactive logon process?
The interactive logon process confirms the user's identification by using the security account database on the user's local computer or by using the domain's directory service. This mandatory logon process cannot be turned off for users in a domain.
How do you log into Windows?
Go to Microsoft account and select Sign in. Type the email, phone number, or Skype sign-in that you use for other services (Outlook, Office, etc.), then select Next. If you don't have a Microsoft account, you can select No account? Create one!.
What happens if you end Windows logon application?
If you try to end the process from the Task Manager, you'll see a message saying that ending the process “will cause Windows to become unusable or shut down”. If you bypass this message, your screen will go black and your PC won't even respond to Ctrl+Alt+Delete.
What is a logon server?
If your computer is connected to domain or workgroup then LOGONSERVER means the group or domain to which your computer is connected.
What is the process of authentication called?
The process of determining claimed user identity by checking user-provided evidence is called authentication and the evidence which is provided by the user during process of authentication is called a credential. Read More News on. AUTHENTICATION. IDENTIFICATION.
What is the process of authentication?
Authentication is the process of determining whether someone or something is, in fact, who or what it says it is. Authentication technology provides access control for systems by checking to see if a user's credentials match the credentials in a database of authorized users or in a data authentication server.
Does Windows authentication use Active Directory?
Windows Authentication is used for servers that run on a corporate network using Active Directory domain identities or Windows accounts to identify users. Windows Authentication is best suited to intranet environments where users, client apps, and web servers belong to the same Windows domain.
What happens if you end Windows logon application?
If you try to end the process from the Task Manager, you'll see a message saying that ending the process “will cause Windows to become unusable or shut down”. If you bypass this message, your screen will go black and your PC won't even respond to Ctrl+Alt+Delete.
What is Advapi logon process?
The logon process is marked as "advapi", which means that the logon was a Web-based logon through the IIS web server and the advapi process. If you are not hosting IIS websites, this might mean that the computer is infected.
What are logon types?
In this articleLogon type#Authenticators acceptedInteractive (also known as, Logon locally)2Password, Smartcard, otherNetwork3Password, NT Hash, Kerberos ticketBatch4Password (stored as LSA secret)Service5Password (stored as LSA secret)3 more rows•Aug 15, 2022
How do I remove winlogon exe virus?
Step 1: Simultaneously press CTRL+ALT+DEL keys to open Task Manager. Step 2: If you notice the file located outside C:\Windows\System32, then you should run an antivirus scan to get rid of the malware.
What Is Windows Logon Application?
The winlogon.exe process is a very important part of the Windows operating system, and Windows will be unusable without it.
Why is Winlogon.exe warning?
High CPU or memory use from winlogon.exe is another warning sign, as this process shouldn’t use much CPU or memory in normal situations.
What is the error code for Winlogon.exe?
If Windows can’t launch winlogon.exe, csrss.exe, or other critical user system processes, your PC will blue screen with error code 0xC000021A.
Is Winlogon running in the background?
Advertisement. In summary, Winlogon is a critical part of the login process and needs to remain running in the background. Microsoft also provides a more detailed, technical list of Winlogon’s responsibilities, if you’re interested.
Where is Winlogon.exe located?
It’s normal for the winlogon.exe process to always be running on your system. The real winlogon.exe file is located in the C:WindowsSystem32 directory on your system. To verify the real Windows Logon Application is running, right-click it in Task Manager and select “Open file location”.
Is Winlogon.exe a scam?
Tech support scammers have pointed to winlogon.exe and other critical system processes and said “If you see this running on your PC, you have malware”. Every PC has the Windows Logon Application running and that’s just normal. Don’t fall for their scams!
Who is Chris Hoffman?
Chris Hoffman is Editor-in-Chief of How-To Geek. He's written about technology for over a decade and was a PCWorld columnist for two years. Chris has written for The New York Times, been interviewed as a technology expert on TV stations like Miami's NBC 6, and had his work covered by news outlets like the BBC. Since 2011, Chris has written over 2,000 articles that have been read nearly one billion times---and that's just here at How-To Geek.
The goal of the Windows logon process
When you sit down at your computer, your aim is to get to your desktop as fast as possible, so you can start working. But we also need to validate that you've entered a correct username and password to prove you are allowed to use that device. Then, you might want access to resources on your local network, like a file share or printer.
The Windows logon process in detail
Step 1 of the Windows logon process with winlogon.exe, logonUI.exe and lsass.exe
Conclusion
The next time it feels like your logon is a little slow, remember all the things it's doing in the background! In a future blog post, we'll go through Steve's explanation of this process in hybrid environments, where Azure Active Directory also comes into play.
What is the detail pane in Event Viewer?
When Event Viewer is opened, the Detail pane displays the Overview and Summary. We’ll discuss the Summary Viewslater. Select an item from the Navigation pane to see a list of events.
What is Windows event log?
The Windows event log contains logs from the operating system and applications such as SQL Server or Internet Information Services (IIS). The logs use a structured data format, making them easy to search and analyze. Some applications also write to log files in text format. For example, IIS Access Logs.
What is a log in a computer?
Logs are records of events that happen in your computer, either by a person or by a running process. They help you track what happened and troubleshoot problems. The Windows event log contains logs from the operating system and applications such as SQL Server or Internet Information Services (IIS).
What does a warning message mean?
Warning messages indicate an event occurred that might become a problem.
What is a forwarded event?
Forwarded Events – Events forwarded by other computers when the local machine is functioning as a central subscriber.
What is application in a machine?
Application – Information logged by applications hosted on the local machine.
What is the console in computer management?
The Computer Management console provides access to administrative tasks on a local or remote server. To open Event Viewer from Computer Management:
What is LogRhythm?
LogRhythm recognizes that some logs are more important to your organization's operation, security, and compliance than others. In the identification process, more important logs are designated as Events–generally this will be around 10% of your total log activity.
What happens when you use debug logs?
Most devices will generate an order of magnitude greater log volume when set to the Verbose or Debug logging levels. The result of this is system impacting on multiple fronts with the most critical being processing via the MPE and indexing via the Data Indexer (DX). Specifically, while Verbose and Debug logs will inevitably hit Catch All rules, they will not only cause an immense MPE slow down, but also many stalled/disabled rules, spooling, and overall poor performance as they attempt to process through every rule in the policy. In addition to this, indexing will be impacted, whereas the logs cause a backup of spooled reliable persist files, resulting in poor DX performance.
What is LogRhythm Schema?
LogRhythm processes your organization's raw log data and presents it in a way that makes it easier to analyze and protect your network operations. For a complete list of metadata fields that LogRhythm parses, calculates, and derives from raw log data, see the LogRhythm Schema Dictionary and Guide. Note that while all metadata fields are available in the Web Console, not all are available in the Client Console.
What is LogRhythm classification?
LogRhythm uses classifications to group similar log messages into logical containers. These classifications provide organization to vast amounts of log data, making it easier to sort through and understand. Classifications fall under three main categories:
What is Platform Manager?
The Platform Manager receives event data from the Data Processors and the AI Engine. It includes an Alarming and Response Manager (ARM), which evaluates the events against rules for alarms and initiates the appropriate response. The Platform Manager also serves as the central point of access for LogRhythm Enterprise. It houses the databases for events, alerts, and metadata, and includes all the configuration information.
What is AI engine?
The AI Engine (if integrated) evaluates logs using a pattern matching and behavioral rule set that can correlate and detect complex issues such as sophisticated intrusions, insider threats, operational issues, and compliance issues. If a log triggers one of the AIE rules, the AI Engine generates a new AIE event for the Platform Manager Database.
What is the MPE in a log server?
The Data Processor is the central processing engine for log messages. Its integrated Mediator Server contains the Message Processing Engine (MPE), which is responsible for the following: Assigning a Log Source based on where the log originated.
What is a secret key?
The secret information is a cryptographic shared key derived from the user's password. A shared secret key is symmetric, which means that the same key is used for both encryption and decryption. The following diagram shows the elements and processes required for smart card logon.
What is network logon?
Network logon. A network logon can only be used after user, service, or computer authentication has taken place. During network logon, the process does not use the credentials entry dialog boxes to collect data. Instead, previously established credentials or another method to collect credentials is used.
What is RDP in remote desktop?
RDP manages the credentials that the user enters by using the Remote Desktop Client. Those credentials are intended for the target computer, and the user must have an account on that target computer. In addition, the target computer must be configured to accept a remote connection.
What is domain user account?
Domain user account information and group membership information are used to manage access to domain and local resources.
What is a SAM?
The SAM protects and manages user and group information in the form of security accounts stored in the local computer registry. The computer can have network access, but it is not required. Local user account and group membership information is used to manage access to local resources.
What is a domain credential?
Credentials that the user presents for a domain logon contain all the elements necessary for a local logon, such as account name and password or certificate, and Active Directory domain information. The process confirms the user's identification to the security database on the user's local computer or to an Active Directory domain. This mandatory logon process cannot be turned off for users in a domain.
What is interactive logon?
The logon process begins either when a user enters credentials in the credentials entry dialog box, or when the user inserts a smart card into the smart card reader, or when the user interacts with a biometric device.
