
Is HIPAA a federal law?
Sep 09, 2021 · HIPAA was enacted on August 21, 1996 when President Bill Clinton added his signature and signed the legislation into law. One of the key aims of the legislation was to improve the portability health insurance coverage – Ensuring employees retained health insurance coverage when between jobs.
What are the rules of HIPAA?
Mar 21, 2019 · President Bill Clinton signed HIPAA into law on August 21, 1996. One of the primary goals of the legislation was to ensure portability health insurance coverage to allow employees to maintain health insurance coverage when they were between jobs.
What is considered protected health information under HIPAA?
Aug 21, 1996 · The most significant effective dates to remember are: August 21, 1996 was the date HIPAA was signed into law. April 14, 2003 for the HIPAA Privacy Rule, although there was an addition of one year for small health plans which were not required to comply with HIPAA Privacy Rule provisions by April 14, 2004. What are the three rules of Hipaa?
What is considered Phi under HIPAA?
The Health Insurance Portability and Accountability Act of 1996 (HIPAA or the Kennedy–Kassebaum Act) is a United States federal statute enacted by the 104th United States Congress and signed into law by President Bill Clinton on August 21, 1996. It modernized the flow of healthcare information, stipulates how personally identifiable information maintained by the …

When was HIPAA first implemented?
Once HIPAA had been signed into law , the US Department of Health and Human Services set about creating the first HIPAA Privacy and Security Rules. The Privacy Rule had an effective compliance date of April 14, 2003, and it defined Protected Health Information (PHI) as “any information held by a covered entity which concerns health status, the provision of healthcare, or payment for healthcare that can be linked to an individual”.
When did HIPAA become effective?
The HIPAA Breach Notification Rule became effective on September 23, 2009 and the Omnibus Final Rule became effective on March 26, 2013.
What is the most recent act of legislation in HIPAA history?
The rule barely introduced any new legislation, but filled gaps in existing HIPAA and HITECH regulations – for example, specifying the encryption standards that need to be applied in order to render ePHI unusable, undecipherable and unreadable in the event of a breach.
How long can a patient's health information be held?
The Privacy and Security Rules were also amended to allow patient´s health information to be held indefinitely (the previous legislation had stipulated it be held for fifty years), while new procedures were written into the Breach Notification Rule.
Why was HIPAA created?
HIPAA was created to “improve the portability and accountability of health insurance coverage” for employees between jobs. Other objectives of the Act were to combat waste, fraud and abuse in health insurance and healthcare delivery. The Act also contained passages to promote the use of medical savings accounts by introducing tax breaks, ...
How does secure messaging improve healthcare?
Many healthcare organizations have reported that the implementation of secure messaging solutions has increased productivity by streamlining communications, increasing message accountability and accelerating response times. According to studies conducted in HIPAA-compliant medical facilities, efficiency has also increased, resulting in a higher standard of healthcare being delivered to patients.
What is the purpose of the Health Information Technology for Economic and Clinical Health Act?
This particular part of the Act spawned the Health Information Technology for Economic and Clinical Health Act (HITECH) in 2009, which in turn lead to the introduction of the Meaningful Use incentive program – described by leaders in the healthcare industry as “the most important piece of healthcare legislation to be passed in the last 20 to 30 years”.
When did HIPAA become law?
HIPAA became a law in 1996 , but over the years, there have been significant revisions to HIPAA legislation, particularly the addition of the HIPAA Privacy Rule, the HIPAA Security Rule, the inclusion of HITECH Act requirements in the HIPAA Omnibus Rule.
When was HIPAA enacted?
The HIPAA Security Rule was initially proposed on August 12, 1998, and enacted on February 20, 2003. Its effective date was April 21, 2006.
What is the HIPAA breach notification rule?
With the integration of the HITECH Act into HIPAA, the HIPAA Breach Notification Rule was created, which required covered entities to inform individuals whose PHI has been exposed or stolen. The HITECH Act additionally mandated business associates of HIPAA-covered entities abide by HIPAA Rules and made them responsible for their own HIPAA violations.
What is the HIPAA Privacy Rule?
The HIPAA Privacy Rule specified the definition of protected health information (PHI) and dictated how HIPAA covered entities could use PHI, to whom PHI could be disclosed, and the circumstances where disclosures were permitted without first obtaining authorizations from patients.
How did HIPAA revisions help?
These revisions put in numerous new terms into HIPAA legislation and helped to ensure the privacy of health data, ensured healthcare organizations implemented appropriate security measures, and ensured that in the event of a breach of protected health information, patients would be notified so they could take steps to reduce the potential for harm.
Why is HIPAA important?
HIPAA additionally helped to reduce wastage in the healthcare industry and helped to prevent fraud and abuse and streamlined the management of healthcare.
When was the HIPAA final rule issued?
December 20, 2000 – Issuance of the HIPAA Final Privacy Rule
What is the HIPAA rule?
HIPAA Security Rule. The Health Insurance Portability and Accountability Act of 1996 (HIPAA) is a federal law that required the creation of national standards to protect sensitive patient health information from being disclosed without the patient’s consent or knowledge. The US Department of Health and Human Services (HHS) issued ...
Who enforces HIPAA rules?
The HHS Office for Civil Rights enforces HIPAA rules, and all complaints should be reported to that office. HIPAA violations may result in civil monetary or criminal penalties. For more information, visit the Department of Health and Human Services HIPAA website. external icon.
What is the HIPAA Privacy Rule?
The Privacy Rule standards address the use and disclosure of individuals’ health information (known as “protected health information”) by entities subject to the Privacy Rule. These individuals and organizations are called “covered entities.”. The Privacy Rule also contains standards for individuals’ rights to understand ...
What are the types of entities that are covered by HIPAA?
The following types of individuals and organizations are subject to the Privacy Rule and considered covered entities: 1 Healthcare providers: Every healthcare provider, regardless of size of practice, who electronically transmits health information in connection with certain transactions. These transactions include claims, benefit eligibility inquiries, referral authorization requests, and other transactions for which HHS has established standards under the HIPAA Transactions Rule. 2 Health plans: Entities that provide or pay the cost of medical care. Health plans include health, dental, vision, and prescription drug insurers; health maintenance organizations (HMOs); Medicare, Medicaid, Medicare+Choice, and Medicare supplement insurers; and long-term care insurers (excluding nursing home fixed-indemnity policies). Health plans also include employer-sponsored group health plans, government- and church-sponsored health plans, and multi-employer health plans.#N#Exception: A group health plan with fewer than 50 participants that is administered solely by the employer that established and maintains the plan is not a covered entity. 3 Healthcare clearinghouses: Entities that process nonstandard information they receive from another entity into a standard (i.e., standard format or data content), or vice versa. In most instances, healthcare clearinghouses will receive individually identifiable health information only when they are providing these processing services to a health plan or healthcare provider as a business associate. 4 Business associates: A person or organization (other than a member of a covered entity’s workforce) using or disclosing individually identifiable health information to perform or provide functions, activities, or services for a covered entity. These functions, activities, or services include claims processing, data analysis, utilization review, and billing.
What is the opportunity to agree or object to disclosure of PHI?
Opportunity to agree or object to the disclosure of PHI (Informal permission may be obtained by asking the individual outright, or by circumstances that clearly give the individual the opportunity to agree, acquiesce, or object)
Does HIPAA apply to PHI?
The Security Rule does not apply to PHI transmitted orally or in writing. To comply with the HIPAA Security Rule, all covered entities must do the following: Ensure the confidentiality, integrity, and availability of all electronic protected health information.
Can a covered entity disclose health information without an individual's authorization?
A covered entity is permitted, but not required, to use and disclose protected health information, without an individual’s authorization, for the following purposes or situations: Disclosure to the individual (if the information is required for access or accounting of disclosures, the entity MUST disclose to the individual) ...
When was HIPAA signed into law?
Signed into law by President Bill Clinton on August 21, 1996. The Health Insurance Portability and Accountability Act of 1996 ( HIPAA or the Kennedy – Kassebaum Act) is a United States federal statute enacted by the 104th United States Congress and signed into law by President Bill Clinton on August 21, 1996.
When was HIPAA updated?
In January 2013, HIPAA was updated via the Final Omnibus Rule. The updates included changes to the Security Rule and Breach Notification portions of the HITECH Act. The most significant changes related to the expansion of requirements to include business associates, where only covered entities had originally been held to uphold these sections of the law.
How many HIPAA violations were there between 2003 and 2013?
According to the US Department of Health and Human Services Office for Civil Rights, between April 2003 and January 2013, it received 91,000 complaints of HIPAA violations, in which 22,000 led to enforcement actions of varying kinds (from settlements to fines) and 521 led to referrals to the US Department of Justice as criminal actions. Examples of significant breaches of protected information and other HIPAA violations include:
What is the title of HIPAA?
Title I of HIPAA regulates the availability and breadth of group health plans and certain individual health insurance policies. It amended the Employee Retirement Income Security Act, the Public Health Service Act, and the Internal Revenue Code.
What is a Title I health plan?
Title I requires the coverage of and also limits restrictions that a group health plan can place on benefits for preexisting conditions. Group health plans may refuse to provide benefits in relation to preexisting conditions for either 12 months following enrollment in the plan or 18 months in the case of late enrollment. Title I allows individuals to reduce the exclusion period by the amount of time that they have had "creditable coverage" before enrolling in the plan and after any "significant breaks" in coverage. "Creditable coverage" is defined quite broadly and includes nearly all group and individual health plans, Medicare, and Medicaid. A "significant break" in coverage is defined as any 63-day period without any creditable coverage. Along with an exception, allowing employers to tie premiums or co-payments to tobacco use, or body mass index.
How long does it take to get a copy of a PHI?
After an individual requests information in writing (typically using the provider's form for this purpose), a provider has up to 30 days to provide a copy of the information to the individual. An individual may request the information in electronic form or hard-copy, and the provider is obligated to attempt to conform to the requested format. For providers using an electronic health record ( EHR) system that is certified using CEHRT (Certified Electronic Health Record Technology) criteria, individuals must be allowed to obtain the PHI in electronic form. Providers are encouraged to provide the information expediently, especially in the case of electronic record requests.
What is the Health Insurance Portability and Accountability Act?
Health Insurance Portability and Accountability Act of 1996. An Act To amend the Internal Revenue Code of 1996 to improve portability and continuity of health insurance coverage in the group and individual markets, to combat waste, fraud, and abuse in health insurance and health care delivery, to promote the use of medical savings accounts, ...
When was HIPAA first introduced?
When was the HIPAA Privacy Rule Introduced? Legislators first proposed the HIPAA Privacy Rule on November 3, 1999, but only enacted the HIPAA Final Privacy Rule of HIPAA enacted on December 20, 2000. HIPAA covered entities were required to comply with the Privacy Rule from April 14, 2003.
Why was HIPAA created?
Legislators originally designed HIPAA to ensure that people who were temporarily out of work would still have access to health insurance. HIPAA has evolved since then to include rules on patient data privacy, data security in the healthcare industry, and data breach responses. HIPAA also encourages providers to improve the efficiency ...
What is the HIPAA Privacy Rule?
The HIPAA Privacy Rule defines PHI and informs CEs and BAs of their responsibilities to protect patient data. The Minimum Necessary Rule is also part of the Privacy Rule, and stipulates that should PHI be handed over to a third party, only the minimum amount of data necessary to complete the specific task should be handed over.
What are the new rules in HIPAA?
These include the Privacy Rule, the Security Rule, the Breach Notification Rule, the Omnibus Rule, and the incorporation of the Health Information Technology for Economic and Clinical Health Act, and the Enforcement Rule.
When was the breach notification rule created?
The Breach Notification Rule was created when the Health Information Technology for Economic and Clinical Health (HITECH) Act was incorporated into HIPAA on February 17, 2009. HITECH was enforceable from February 27, 2010. The Breach Notification Rule outlines procedures that must be followed in the aftermath of a breach to ensure that the risk ...
When did CEs have to comply with HIPAA?
CEs had to comply with the HIPAA Security Rule from April 21, 2006. The HIPAA Security Rule outlines the minimum physical, technical, and administrative safeguards needed to protect electronic PHI.
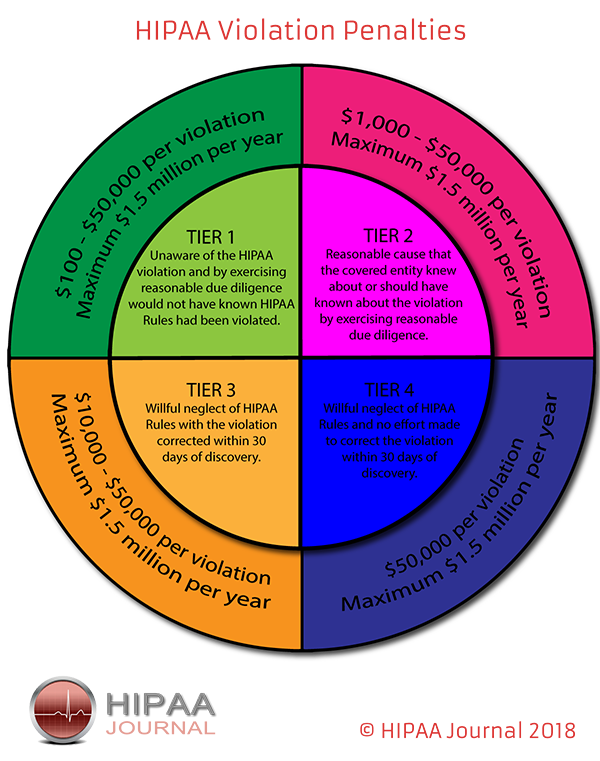
When was the Enforcement Rule finalized?
The Enforcement Rule was first proposed on April 18, 2005, and finalised on February 16, 2006. The Enforcement Rule contains guidance on the fines and penalties that may be levied against a CE should a data breach occur. (OCR and Department of Health and Human Services can alter punishments at their discretion.)
When did HIPAA become law?
On August 21, 1996 , in the midst of his re-election campaign, President Bill Clinton signed HIPAA into law. The U.S. Congress generally does not, when legislating, consider much of the finer or granular details of how a law should work, logistically.
When did HIPAA go into effect?
In March of 2006, the HIPAA Enforcement Rule went into effect, heralding, essentially, the beginning of HIPAA compliance enforcement. OCR is given the authority to enforce the HIPAA Rules by imposing financial penalties against non-compliant entities.
What is the third HIPAA rule?
This rule, known as the Breach Notification Rule, requires covered entities to report data breaches to OCR, and to provide notice of a breach to individuals affected by the breach.
When did the HIPAA Omnibus rule become effective?
The HIPAA Omnibus Rule, containing modifications to the Privacy, Security, Breach Notification, and Enforcement Rule, is finalized in 2012. The final Omnibus Rule becomes effective in 2013, and contains modifications to improve data security and confidentiality. Notably, under the Omnibus Rule, business associates are directly liable for HIPAA violations. Under the Omnibus Rule, business associate compliance with the Privacy Rule and the Security Rule becomes mandatory.
When did HHS make the HIPAA corrections?
A notable correction created a requirement mandating that OCR enforce HIPAA. The technical corrections became effective in early 2001, when George W. Bush was President. The Bush administration decided to seek further input on the Privacy Rule. In other words, as part of the rulemaking process, HHS allowed the public to make comments on what modifications, if any, should be made to the Privacy Rule. HHS took note of the comments received and issued a Proposed Modified Privacy Rule in 2002. The proposed modified rule contained provisions designed to reduce administrative burdens on healthcare providers. Finally, in 2003, the Privacy Rule was finalized. Covered entity compliance was required by April 14 of 2003.
When did HHS start requiring PHI?
The rule required covered entity compliance by April of 2005. In 1999, HHS proposed the Privacy Rule. The proposed rule sought to improve privacy standards and to restrict the disclosure of PHI and personal identifiers to unauthorized individuals. The rule also sought to give patients better access to their health data.
How many times has HIPAA been amended?
The law and its implementing regulations have been amended a number of times in 23 years. The HIPAA history timeline is presented below.
Why does HIPAA matter?
Why does HIPAA matter? Well, all healthcare entities and organizations that use, store, maintain or transmit patient health information are expected to be in complete compliance with the regulations of the HIPAA law. When completely adhered to, HIPAA regulations not only ensure privacy, reduce fraudulent activity and improve data systems but are estimated to save providers billions of dollars annually. By knowing of and preventing security risks that could result in major compliance costs, organizations are able to focus on growing their profits instead of fearing these potential audit fines.
What records are protected by privacy laws?
The United States Congress had many privacy regulations protecting fields such as school records, driver license records and even video rental records but nothing pertaining to the privacy of personal health information.
When will HIPAA be implemented?
A Brief History of the HIPAA Law. April 1, 2019. May 3, 2021. HIPAA law is used in every pharmacy, medical office, health insurance company, and more. But did you know that the original goal of HIPAA was not to protect electronic patient information at all?
When did HIPAA expand?
HIPAA laws expanded again in 2009 with the introduction of the Health Information Technology for Economic and Clinical Health Act, or HITECH. HITECH furthered the expansion and use of EHR, or electronic health records. This provision also led to the creation of the Breach Notification Rule.
What was the purpose of the Health Insurance Portability and Accountability Act?
The intent was to “improve the portability and accountability of health insurance coverage.”. The other provisions included sections on waste management, health insurance fraud, and abuse. HIPAA also created tax breaks for medical savings ...
What are the three safeguards created by HIPAA?
The three safeguards created by HIPAA Security were physical, administrative, and technical.
When was PHI created?
After HIPAA became law , the Health and Human Services Department created the first rules for Privacy and Security. As of April 14, 2003, HIPAA Privacy defined PHI (Protected Health Information) as “any information held by a covered entity which concerns health status, the provision of healthcare, or payment for healthcare that can be linked to an individual.”
What was the movement after the passage of HIPAA?
Only after the passage of HIPAA was there a movement to streamline the digital conversion of patient medical files. These digital files needed protection from privacy violations.
What were the other provisions of HIPAA?
The other provisions included sections on waste management, health insurance fraud, and abuse. HIPAA also created tax breaks for medical savings accounts, pre-existing conditions coverage, and improved health insurance administration. Only after the passage of HIPAA was there a movement to streamline the digital conversion of patient medical files.
Purpose
- Our HIPAA history lesson starts on August 21, 1996, when the Healthcare Insurance Portability and Accountability Act (HIPAA) was signed into law, but why was the HIPAA act created? HIPAA was created to improve the portability and accountability of health insurance coverage for employees between jobs. Other objectives of the Act were to combat waste, fraud and abuse in …
Content
- Instructions were issued on how PHI should be disclosed and that permission should be sought from patients before using their personal information for marketing, fundraising or research. It also gave patients the right to withhold information about their healthcare from health insurance providers when their treatment is privately funded.
Timeline
- In what year was HIPAA signed into law? HIPAA was signed into law on August 21, 1996, but there have been major additions to HIPAA over the past 20 years: The introduction of the Privacy Rule, Security Rule, Breach Notification Rule, and the Omnibus Final Rule.
Schedule
- The most important effective dates are: April 14, 2003 for the HIPAA Privacy Rule, although there was an extension of one year for small health plans, that were required to comply with the HIPAA Privacy Rule provisions by April 14, 2004.
Security
- The failure of many covered entities to fully comply with the HIPAA Privacy and Security Rules resulted in the introduction of the Enforcement Rule in March 2006. The Enforcement Rule gave the Department of Health and Human Services the power to investigate complaints against covered entities for failing to comply with the Privacy Rule, and to fine covered entities for avoid…
Functions
- The Department´s Office for Civil Rights was also given the power to bring criminal charges against persistent offenders who fail to introduce corrective measures within 30 days. Individuals also have the right to pursue civil legal action against the covered entity if their personal healthcare information has been disclosed without their permission if it causes them to come t…
Scope
- Many definitions were amended or added to clear up grey areas for example the definition of workforce was changed to make it clear that the term includes employees, volunteers, trainees, and other persons whose conduct, in the performance of work for a covered entity or Business Associate, is under the direct control of the covered entity or Business Associate. Our HIPAA Co…
Significance
- The Privacy and Security Rules were also amended to allow patient´s health information to be held indefinitely (the previous legislation had stipulated it be held for fifty years), while new procedures were written into the Breach Notification Rule. New penalties were also applied as dictated by HITECH to covered entities that fell afoul of the HIPAA Enforcement Rule. Amendme…
Goals
- What the Final Omnibus Rule achieved more than any previous legislation was to make covered entities more aware of HIPAA safeguards that they had to adhere to. Many healthcare organizations who had been in breach of HIPAA for almost two decades implemented a number of measures to comply with the regulations, such as using data encryption on portable devices a…
Cost
- The financial penalties now being issued for data breaches along with the colossal costs of issuing breach notifications, providing credit monitoring services and conducting damage mitigation makes investment in new technology to protect data appear cheap by comparison. The move from physical health records to electronic data formats has required considerable investm…
Prevention
- The use of laptop computers and other mobile devices for storing or accessing ePHI inevitably results in a HIPAA breach if those devices are lost, stolen or improperly recycled. Password protection of devices and the data they contain is a reasonable step to prevent unauthorized access, but alone it is insufficient to provide the necessary protection for health data. Password…
Summary
- Data encryption involves the conversion of data into indecipherable symbols termed cipher text by complex algorithms, that require a security key to convert the data back into its original form. Data encryption ensures privacy, but can offer other security benefits such as verification of users, access logging, the prevention of record changes and non-repudiation of access and/or theft.
Advantages
- Secure messaging solutions prevent this. They work by maintaining ePHI on a secure database and then allowing authorized medical professionals to access the data via downloadable secure messaging apps. Communications are channeled through a secure messaging platform which has administrative controls in place to monitor the activity of the authorized personnel. They als…
Impact
- Many healthcare organizations have reported that the implementation of secure messaging solutions has increased productivity by streamlining communications, increasing message accountability and accelerating response times. According to studies conducted in HIPAA-compliant medical facilities, efficiency has also increased, resulting in a higher standard of healt…
Technology
- The computer equipment now required to run large networks and store healthcare data requires cooling systems to be installed to dissipate the heat the equipment generates. The most cost effective solution for many healthcare providers is to outsource data storage and take advantage of the cloud to store data. HIPAA-compliant cloud hosting employs the appropriate controls to s…
Applications
- Mobile health apps are popular with patients for tracking and monitoring health and fitness, and wearable devices have potential to revolutionize home healthcare. They can be used in conjunction with e-visits to provide home care services to patients at a fraction of the healthcare center visits.
Benefits
- Patient portals similarly have great potential and improve interaction between care providers and patients, and cut down on unnecessary costs while helping to improve patient outcomes. The development of HIPAA compliant mobile apps frameworks, compliant storage and HIPAA compliant web solutions means healthcare providers can take advantage of the benefits of new …
Future
- More technical safeguards to secure ePHI and personal identifiers are no doubt in the planning stage now and will impact HIPAA history in the future. In the meantime, here is a brief HIPAA history timeline.
Hipaa Privacy Rule
Covered Entities
- The following types of individuals and organizations are subject to the Privacy Rule and considered covered entities: 1. Healthcare providers: Every healthcare provider, regardless of size of practice, who electronically transmits health information in connection with certain transactions. These transactions include claims, benefit eligibility inquiries, referral authorizatio…
Permitted Uses and Disclosures
- A covered entity is permitted, but not required, to use and disclose protected health information, without an individual’s authorization, for the following purposes or situations: 1. Disclosure to the individual (if the information is required for access or accounting of disclosures, the entity MUST disclose to the individual) 2. Treatment, payment, and healthcare operations 3. Opportunity to ag…
Hipaa Security Rule
- While the HIPAA Privacy Rule safeguards protected health information (PHI), the Security Rule protects a subset of information covered by the Privacy Rule. This subset is all individually identifiable health information a covered entity creates, receives, maintains, or transmits in electronic form. This information is called “electronic protected health information” (e-PHI). The …