- It brings in the much-needed regulation in the market required for cryptographic tokens.
- As a result, such projects will have more support from the investors and will have their trust.
- This will bring more liquidity to the securities market.
- Will be more cost-effective, secure, & fast in trading.
What is a security token?
Every security token contains a tiny bit of data that could be considered a password. It isn't always entered into a system via a keypad or scanner, but the token completes some type of secure data exchange with the resource the user is trying to access.
What are the advantages and disadvantages of security tokens?
While security tokens offer a variety of advantages to users and organizations, they can introduce disadvantages as well. The main disadvantage of physical security tokens is that they are subject to loss and theft. For example, a security token could be lost while traveling or stolen by an unauthorized party.
Why should I use an access token instead of an ID token?
This article is an attempt to clear what is what and explain why you should always use an access token to secure an API, and never an ID token. OAuth 2.0 is used to grant authorization. It enables you to authorize the Web App A to access your information from Web App B, without sharing your credentials.
What is a disconnected token used for?
This is a form of digital security token that does not connect physically or logically to a computer. The device may generate an OTP or other credentials. A desktop application that sends a text message to a cellphone, which the user must input in the login, is using a disconnected token. Connected tokens.
Why we use token based authentication?
It enables users to verify their identity to websites, which then generates a unique encrypted authentication token. That token provides users with access to protected pages and resources for a limited period of time without having to re-enter their username and password.
How do security tokens work Crypto?
Security tokens are digital assets that represent transferred ownership rights or asset value to a blockchain token. A security token is created using tokenization, where the investment criteria are selected. The information is entered into the blockchain, which then creates a token.
Why are tokens more secure?
Tokens Offer Robust Security Since tokens like JWT are stateless, only a secret key can validate it when received at a server-side application, which was used to create it. Hence they're considered the best and the most secure way of offering authentication.
What is a security token example?
Car remotes are examples of security tokens people use regularly. Security tokens are used to authenticate users, and they can be used either to substitute passwords or other authentication methods or used as additional authentication in multi-factor authentication (MFA) flow.
Are NFTs security tokens?
These security tokens are offered to the public in a way that is compliant with the federal securities laws´ registration provisions. Individuals and businesses that issue non-fungible tokens (NFTs) may have to register their NFTs as securities.
Which Cryptos are security tokens?
Just like utility tokens, most security tokens run on the Ethereum blockchain. However, other smart contract-enabled blockchains also support them. The tokens can come in a variety of forms, from shares of ownership in a company, piece of art, intellectual property, or any other kind of asset.
Why are tokens more secure than passwords?
Tokens essentially act as an extra layer of security and serve as a temporary stand-in for the user's password. Most importantly, tokens are machine-generated. Encrypted, machine-generated code is significantly more secure than any password you might create yourself.
Why are tokens better than password?
During the life of the token, users then access the website or app that the token has been issued for, rather than having to re-enter credentials each time they go back to the same webpage, app, or any resource protected with that same token.
Are tokens more secure than passwords?
Tokens can represent authorization on a much finer scale. A username and password can be used to request a very limited token. A password might be good for 90 days or more, but a token could be issued that lasts only three minutes, making them harder to exploit.
Can security token be hacked?
Hacking. Tokens should protect users from malware, and companies like banks often tell their customers token systems are safer for that reason. But anything that's electronic and connected to a network can be hacked by someone with skill and patience.
What are the best security tokens?
Top Security Token PlatformstZERO.INX.ADDX.Nxchange.
How does a token work?
How do tokens work? In many cases, tokens are created via dongles or key fobs that generate a new authentication token every 60 seconds in accordance with a known algorithm. Due to the power these hardware devices hold, users are required to keep them safe at all times to ensure they don't fall into the wrong hands.
Can you trade security tokens?
Security Tokens and Taxation If you trade any blockchain tokens, you should comply with securities regulations. Those tokens are probably investment products, and your profits and losses from trading security tokens will likely be taxed as investment income, and you should approach them as such.
What does it mean if crypto is a security?
Echoing his predecessor's sentiments, current SEC Chair Gary Gensler reiterated to CNBC in August 2021 that the SEC considers many cryptocurrency coins and tokens to be securities under the Howey Test, saying, "If somebody is raising money selling a token and the buyer is anticipating profits based on the efforts of ...
How do I create a security token?
How to create a security token and run an STOSection one: Decide what rights the security token provides.Section two: Choose which jurisdiction to operate in.Section three: Choose a security token issuance platform.Section four: Create the token.Section five: Run the security token offering.
How do I invest in security tokens?
To wrap it up here are the quick steps to buying security tokens:Use STOmarket.com to find the security token you're looking to buy.Click the invest button and you will be routed to the exchange on which that token is trading.Register on that exchange.Purchase that security token.
What is a security token?
To understand what a security token is, you must first know what a utility token is. Most tokens issued by blockchain projects so far are utility tokens. A utility token is ‘a token that grants user rights of the services or goods provided by a certain network’ (the detailed definition of a utility token can vary from perspective). The usage value of a utility token is determined by the ‘rights’ bestowed by the protocol.
Why are security tokens better than ICOs?
Fundraising through security tokens has more benefits compared to ICOs utilizing utility tokens because ICOs rendered significant side effects for being rampant without regulation. The key benefits of STOs are that they 1) secure safety for investors and have 2) possible influx of institutional investors.
Does Deacon Solar issue tokens?
However, the situation would be different if Deacon Solar carries out an STO. Aside from its utility token Solar, Deacon Solar would issue a security token ‘Solar Fund Token’ for fundraising purposes. Investors who see investment value in Deacon Solar would help the company’s fundraising by purchasing Solar Fund Tokens and acquire shares of the company. If they forecast a grim outlook for Deacon Solar, they would sell their Solar Fund Tokens.
Can security tokens be used for fundraising?
The benefits of introducing security tokens in blockchain projects are not confined to fundraising. In the case of ICOs, utility tokens that will actually be used on the network are used for fundraising.
Is there a legal standard for security tokens?
There are no clear regulations on security tokens including taxation and KYC, and there is yet to be a complete technological standard for security tokens.
How does a security token work?
Security token technology is based on the use of a device that generates a random number, encrypts it and sends it to a server with user authentication information. The server then sends back an encrypted response that can only be decrypted by the device. The device is reused for every authentication, so the server does not have to store any username or password information, with the intent of making the system less vulnerable to hacking.
What is a security token?
A security token is a physical or digital device that provides two-factor authentication ( 2FA) for a user to prove their identity in a login process. It is typically used as a form of identification for physical access or as a method of computer system access. The token can be an item or a card that displays or contains security information about a user and can be verified by the system.
What are the disadvantages of physical security tokens?
The main disadvantage of physical security tokens is that they are subject to loss and theft. For example, a security token could be lost while traveling or stolen by an unauthorized party. If a security token is lost or stolen, it must be deactivated and replaced. In the meantime, an unauthorized user in possession of the token may be able to access privileged information and systems.
Is a password a security token?
While it's true that passwords and user IDs are still the most widely used form of authentication, security tokens are a more secure option for protecting networks and digital systems. The trouble with passwords and user IDs is that they are not always secure. Threat actors continue to refine methods and tools for password cracking, making passwords vulnerable. Password data may also be accessed or stolen in a data breach. In addition, passwords are often easy to guess, usually because they are based on easily discoverable personal information.
What is a security token?
In simpler terms, security tokens are cryptographic tokens that pay dividends, share profits, pay interest or invest in other tokens or assets to generate profits for the token holders. This takes care of the liquidity issues.
What are the elements of security?
A security is found to exist when all four of these elements exist: 1 Investment of money 2 In a common enterprise 3 With an expectation of profits 4 From the efforts of others
What is securities in finance?
Securities are tradable financial assets such as bonds, debentures, notes, options, shares (stocks), and warrants. And if we take the example of stocks, you might understand that it is a way to own a part in a company without taking actual possession of it.
Can blockchains be used for smart contracts?
Lastly, more and more companies want to leverage the power of blockchains, smart contracts in their business which they can surely do through such programmable security tokens
Is liquidity a problem with tokens?
Previously, with traditional paper backed assets like company’s shares or bonds or real estate, liquidity was a problem, but the cryptographic representation of all these things in a token form can take care of that issue.
What Is a Security Token?
A security token is a portable device that authenticates a person's identity electronically by storing some sort of personal information. The owner plugs the security token into a system to grant access to a network service. Security Token Services (STS) issue security tokens that authenticate the person's identity.
Why do security tokens store data?
Also, security tokens store data in order to authenticate the owners' identities. Some store cryptographic keys, a system used in cryptocurrency services such as Bitcoin, but the key must be kept secret. Some use time-sensitive passwords, which are coordinated between the token and the network and are reset at constant intervals. Others use biometrics such as fingerprint data to ensure that only the owner of the security token can access protected information.
What is a single sign on service?
Single sign-on services also use security tokens to log users into third-party websites seamlessly. Disconnected tokens are not linked to the computer or network in any way; rather, the user enters the information from the token manually into the system. Connected tokens work electronically and automatically transmit information to the network once they're connected.
What is time sensitive password?
Some use time-sensitive passwords, which are coordinated between the token and the network and are reset at constant intervals. Others use biometrics such as fingerprint data to ensure that only the owner of the security token can access protected information.
Can security tokens be hacked?
Security tokens can also be hacked. This often happens when the owner unknowingly provides sensitive information to an unauthorized provider who then inputs the information into the secure network. This is known as man-in-the-middle fraud. Any network connected to the Internet is vulnerable to such an attack.
Is a security token always secure?
Security tokens are not always secure—they may be lost, stolen, or hacked.
Can you use a security token to access a service?
As with any system, security tokens are not flawless. If the token is lost or stolen or if it isn't in the owner's possession, it cannot be used to access a service. However, the owner can take steps to prevent loss or theft, such as locks or alarms, and the token can be rendered useless to a thief by using two-factor authentication, which requires both an item in the owner's possession (for example, a bank card) and a piece of knowledge (for example, a PIN) to access the token.
What is an ID token?
The id_token is a JWT and is meant for the client only. In the example we used earlier, when you authenticate using Google, an id_token is sent from Google to the to-do application, that says who you are.
What is access token?
The access_token can be any type of token (not necessarily a JWT) and is meant for the API. Its purpose is to inform the API that the bearer of this token has been authorized to access the API and perform specific actions (as specified by the scope that has been granted).
What is a token in API?
This token is meant for authorizing the user to the API. As such, it is completely opaque to clients, meaning that a client should not care about the contents of this token, decode it or depend on a particular token format. Note that the token does not contain any information about the user itself besides their ID ( sub claim), it only contains authorization information about which actions the client is allowed to perform at the API ( scope claim).
What is an aud claim token?
This token is meant for authenticating the user to the client. Note that the audience ( aud claim) of the token is set to the client's identifier, which means that only this specific client should consume this token.
Can you trust an API token?
If it isn't you shouldn't trust the token. An API, on the other hand, expects a token with the audience set to the API's unique identifier. So unless you are in control of both the client and the API, sending an id_token to an API will not work.
Is an access token opaque?
Note: Access Tokens should be treated as opaque strings by clients. They are only meant for the API. Your client should not attempt to decode them or depend on a particular access_token format.
Can you use id_token to validate a JWT?
Note: You must never use the info in an id_token unless you have validated it! For more information refer to: How to validate an ID token. For a list of libraries you can use to verify a JWT refer to JWT.io.

Tokens in The World of Cryptocurrencies – What Are They?
- Before we discuss security tokens, let’s analyze the actual definition of a token and its role in the cryptocurrency world. As defined, a token is a digital unit that represents an accepted value. Based on the function that tokens perform, we can distinguish three types of tokens: utility, payment, and security tokens.
Tokens vs Cryptocurrencies – What’s The difference?
- What is a token in a cryptocurrency? Let us clarify this point. The termtoken is sometimes used interchangeably with the word cryptocurrency. This is a common mistake – although at first glance they may appear to be the same thing, there are significant differences between them. Firstly, while cryptocurrencies use blockchains created for their purpose, tokens are based on of…
Security Tokens – What Is Their function?
- In spite of their name, security tokens don’t refer to security but to financial values in the form of shares, bonds, or options. These tokens reflect legal ownership, and have a structure resembling security. So what is a security token and what could it represent? A security token can represent a share in a company, voting rights, a unit of value...
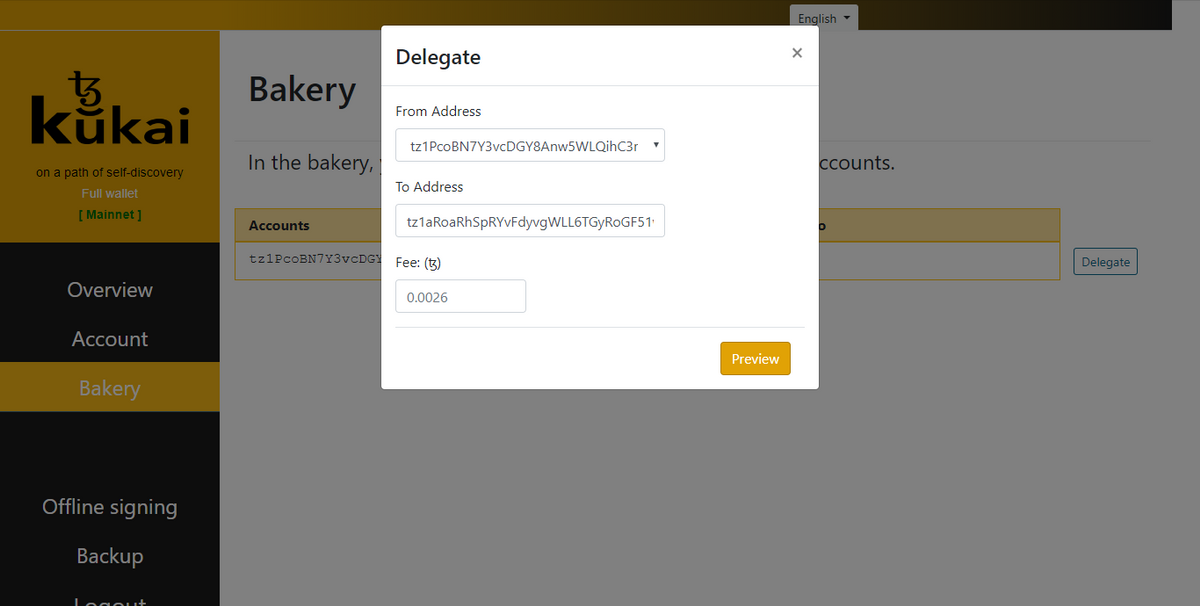
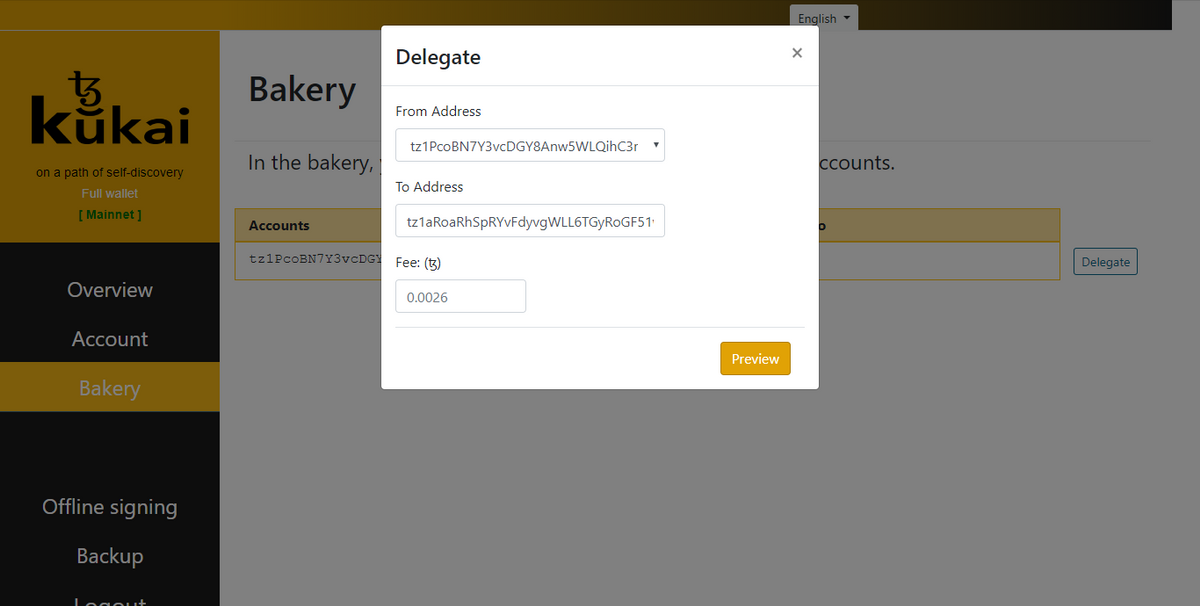
Security Token Offerings (STO) – What Do They Consist of?
- Security Token Offering (STO) is a method of funding blockchain projects that has replaced the previously used ICO (Initial Coin Offering). It aims to increase the security of investors and improve the transparency of the process, compared to traditional models of investing in modern technologies. Companies are required to register STOs with relevant regulatory authorities.In tur…