An SSL/TLS handshake is a negotiation between two parties on a network – such as a browser and web server – to establish the details of their connection. It determines what version of SSL/TLS will be used in the session, which cipher suite will encrypt communication, verifies the server (and sometimes also the client ), and establishes that a secure connection is in place before transferring data.
Full Answer
How to fix SSL handshake problem?
Update the Browser to the Latest Build
- Open the Chrome browser and in the top right corner, click on three vertical ellipses to open the Chrome menu.
- Now select Settings and in the left pane, head to the About Chrome tab.
- Then, in the right pane, make sure the Google Chrome is updated to the latest build, and afterward, check if the SSL handshake error is cleared. ...
How to fix TLS handshake?
How to troubleshoot TLS handshake issues?
- Solution 1: Ensuring the Correct System Time. Most of the time, a TLS handshake fails because of incorrect system time settings. ...
- Solution 2: Changing the TLS Protocol in Windows 10. ...
- Solution 3: Deleting the Certificate Database or Browser Profile. ...
- Solution 4: Resetting Your Browser. ...
How to solve TLS handshake failed error?
Troubleshooting for clients
- Update or change your browser. As a rule, all browsers update TLS protocol, but users often utilize the outdated version of a browser.
- If you use Chrome, then try to turn off the QUICK protocol. In the search line of Google Chrome put in chrome://flags. ...
- Try to deactivate your extensions. ...
- Change WiFi connection. ...
- Clear cache and cookies
How to stop SSL?
- Log into WHM as root
- Go to Home >> SSL/TLS >> Manage AutoSSL
- Go to Manage Users
- From there, you can select "Disable AutoSSL" on the user of your choice.

How SSL TLS handshake works?
The SSL or TLS handshake enables the SSL or TLS client and server to establish the secret keys with which they communicate. This section provides a summary of the steps that enable the SSL or TLS client and server to communicate with each other. Agree on the version of the protocol to use.
What happens after TLS handshake?
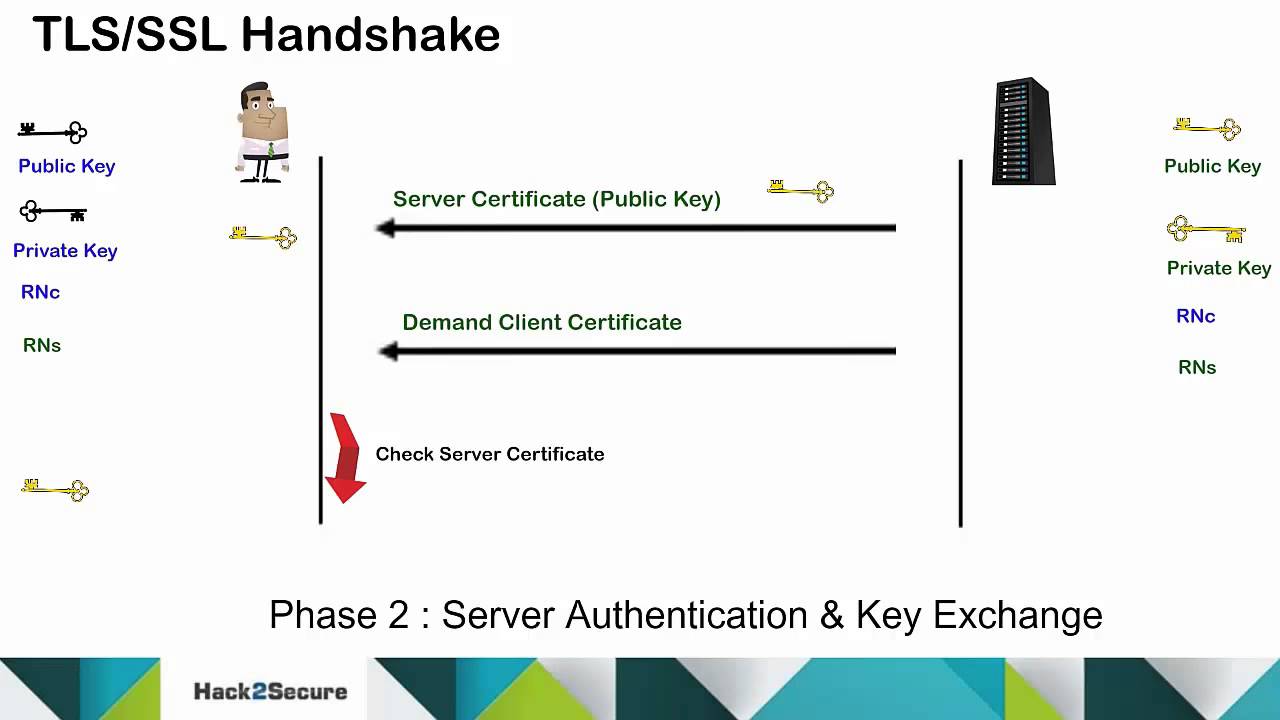
A TLS handshake marks the onset of TLS communication between the client and the server. During a TLS handshake, both the parties exchange messages verify the identity, agree on cipher suite and TLS version to be used in communication, and finally establish the session's keys.
How many steps are in a TLS handshake?
The TLS 1.2 Handshake: Step by Step. Each TLS handshake involves a series of steps, which accomplish the three main tasks we summarized above: exchanging encryption capabilities, authenticating the SSL certificate, and exchanging/generating a session key.
Is TLS handshake encrypted?
Inside the TLS Handshake. The goal of the TLS handshake is for the client and the server to agree on a shared symmetric encryption key in a secure fashion. To do so, they use asymmetric encryption, which allows encrypted messages to be sent using only a public key.
How SSL works step by step?
Step-by-step, here's how SSL works:A user connects to an SSL-enabled service such as a website.The user's application requests the server's public key in exchange for its own public key. ... When the user sends a message to the server, the application uses the server's public key to encrypt the message.More items...
How does exactly TLS work?
SSL uses port number 443, encrypting data exchanged between the browser and the server and authenticating the user. Therefore, when the communications between the web browser and server need to be secure, the browser automatically switches to SSL — that is, as long as the server has an SSL certificate installed.
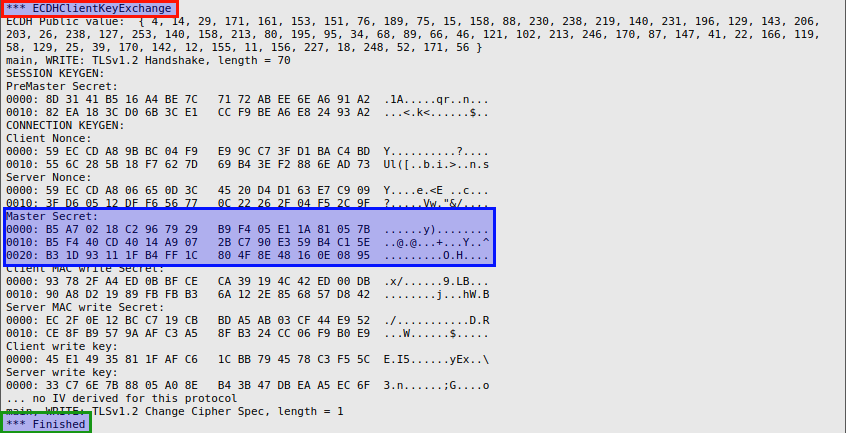
What keys are used in TLS handshake?
The 4 kinds of session keys created in each TLS handshake are: The "client write key" The "server write key" The "client write MAC key"
What is difference between SSL and TLS?
Transport Layer Security (TLS) is the successor protocol to SSL. TLS is an improved version of SSL. It works in much the same way as the SSL, using encryption to protect the transfer of data and information. The two terms are often used interchangeably in the industry although SSL is still widely used.
What is 3 way SSL handshake?
A suite contains three different algorithms: The key exchange and authentication algorithm used during the handshake. The encryption algorithm used to encipher the data. The MAC (Message Authentication Code) algorithm, used to generate the message digest.
Where does TLS handshake happen?
TLS handshake is responsible for establishing a secure connection between a client and a server. When you visit a web site via https, TLS handshake happens between your browser and the web server, so your browser can communicate with web server via a secure connection.
How long does a TLS handshake take?
First, the TLS 1.3 handshake process only requires 1 round trip. Resuming a TLS session is also much faster with TLS 1.3 as this protocol support the “0-RTT round trip” resumption!
How do you know if a SSL is 2 way?
In Two-Way SSL authentication, the client and server need to authenticate and validate each others identities. The authentication message exchange between client and server is called an SSL handshake, and it includes the following steps: A client requests access to a protected resource.
How long does TLS handshake take?
First, the TLS 1.3 handshake process only requires 1 round trip. Resuming a TLS session is also much faster with TLS 1.3 as this protocol support the “0-RTT round trip” resumption!
How does TLS 1.2 handshake work?
A TLS handshake is the process that kicks off a communication session that uses TLS. During a TLS handshake, the two communicating sides exchange messages to acknowledge each other, verify each other, establish the cryptographic algorithms they will use, and agree on session keys.
What is difference between SSL and TLS?
Transport Layer Security (TLS) is the successor protocol to SSL. TLS is an improved version of SSL. It works in much the same way as the SSL, using encryption to protect the transfer of data and information. The two terms are often used interchangeably in the industry although SSL is still widely used.
What is SSL/TLS handshake?
What Is An SSL/TLS Handshake? SSL/TLS are protocols used for encrypting information between two points. It is usually between server and client, but there are times when server to server and client to client encryption are needed. This article will focus only on the negotiation between server and client.
What is a standard SSL handshake?
The following is a standard SSL handshake when RSA key exchange algorithm is used: 1. Client Hello. Information that the server needs to communicate with the client using SSL. This includes the SSL version number, cipher settings, session-specific data. 4. Decryption and Master Secret.
What is Digicert SSL/TLS certificate?
DigiCert SSL/TLS Certificates with Extended Validation (EV) provide solutions that allow companies and consumers to engage in communications and commerce online with confidence.
How many files are needed for SSL/TLS negotiation?
For SSL/TLS negotiation to take place, the system administrator must prepare the minimum of 2 files: Private Key and Certificate. When requesting from a Certificate Authority such as DigiCert Trust Services, an additional file must be created. This file is called Certificate Signing Request, generated from the Private Key. The process for generating the files are dependent on the software that will be using the files for encryption. For a list of the server softwares DigiCert has, look at: DigiCert CSR Generation.
Why do both client and server exchange messages?
Both client and server exchange messages to inform that future messages will be encrypted.
What is the purpose of a private key in a server?
Server uses its private key to decrypt the pre-master secret. Both Server and Client perform steps to generate the master secret with the agreed cipher.
What happens during a TLS handshake?
During the course of a TLS handshake, the client and server together will do the following:
When does a TLS handshake occur?
A TLS handshake takes place whenever a user navigates to a website over HTTPS and the browser first begins to query the website's origin server. A TLS handshake also happens whenever any other communications use HTTPS, including API calls and DNS over HTTPS queries.
What is SSL authentication?
Authentication: The client verifies the server's SSL certificate with the certificate authority that issued it. This confirms that the server is who it says it is, and that the client is interacting with the actual owner of the domain.
What is server hello?
The 'server hello' message: In reply to the client hello message, the server sends a message containing the server's SSL certificate, the server's chosen cipher suite, and the "server random," another random string of bytes that's generated by the server.
What is client hello?
The 'client hello' message: The client initiates the handshake by sending a "hello" message to the server. The message will include which TLS version the client supports, the cipher suites supported, and a string of random bytes known as the "client random."
How are session keys created?
Session keys created: Both client and server generate session keys from the client random, the server random, and the premaster secret. They should arrive at the same results.
What is secure symmetric encryption?
Secure symmetric encryption achieved: The handshake is completed, and communication continues using the session keys. All TLS handshakes make use of asymmetric encryption (the public and private key), but not all will use the private key in the process of generating session keys.
What is an SSL/TLS handshake?
SSL/TLS handshake is the process of establishing a secure connection between a server and a site. This is one of the most critical steps in setting up a secure connection. After a safe connection is established, both the server and client can confidently communicate with each other.
Why do websites use TLS instead of SSL?
Now, almost all websites use TLS instead of SSL because it provides better protection than SSL.
What is the first phase of TLS?
Therefore, the first phase of the TLS handshake enables the user and server to share their resources such that the cryptographic characteristics they collectively support can be identified.
Why do we need SSL certificates?
Web owners frequently use SSL Certificates to keep hackers at bay. To start a secure connection, both the client and the server first conduct an SSL handshake process that includes authentication, key exchange process, etc. Let us first start with SSL/TLS certificates to know their work process. Then we will explain the whole TLS handshake process.
What is a trustworthy SSL certificate?
All trustworthy SSL certificates are granted by the Certificate Authority (CA), an authorized digital certificate issuing agency. Such companies need to follow stringent issuance and certificate protocols so that the licenses they grant are approved. This is mainly to make sure you can only obtain a certificate for a domain or business that you own. In this way, you can assume a CA such as a notary. The signature indicates that the person or organization on the license is who it claims to be.
What is SSL encryption?
An SSL (Secure Socket Layer) is a standard security protocol widely used to secure communication over the internet. SSL uses asymmetric encryption to safeguard the information from the reach of attackers.
Why is SSL important?
SSL Certificate or Digital certificate has become popular due to their security to web users, website owners, and publishers. They utilize public-key cryptography to encode the data transmission between the clients and the webserver. There are various types of digital certificates, but all serve the same process to provide security to both ...
What is SSL handshake?
The SSL or TLS handshake enables the SSL or TLS client and server to establish the secret keys with which they communicate.
What does SSL mean in TLS?
The SSL or TLS client sends the server a finished message, which is encrypted with the secret key, indicating that the client part of the handshake is complete.
What happens when a client sends a certificate request?
If the SSL or TLS server sent a client certificate request, the client sends a random byte string encrypted with the client's private key, together with the client's digital certificate, or a no digital certificate alert. This alert is only a warning, but with some implementations the handshake fails if client authentication is mandatory.
What is a TLS client?
The SSL or TLS client sends a client hello message that lists cryptographic information such as the SSL or TLS version and, in the client's order of preference, the CipherSuites supported by the client. The message also contains a random byte string that is used in subsequent computations. The protocol allows for the client hello to include the data compression methods supported by the client.
Why use asymmetric encryption?
Use asymmetric encryption techniques to generate a shared secret key, which avoids the key distribution problem. SSL or TLS then uses the shared key for the symmetric encryption of messages, which is faster than asymmetric encryption.
Can a TLS server and client exchange encrypted messages?
For the duration of the SSL or TLS session, the server and client can now exchange messages that are symmetrically encrypted with the shared secret key.
What is SSL/TLS handshake?
The SSL/TLS handshake involves a series of steps through which both the parties – client and server, validate each other and start communicating through the secure SSL/TLS tunnel.
Why is SSL handshake called SSL?
SSL Handshake Explained. The reason it’s called a handshake is that it’s when two parties – client and server come across each other for the first time. The handshake involves a number of steps that start from validating the identity of the other party and concludes with the generation of a common key – secret key if you may call it.
What is TLS handshake?
TLS communication sessions begin with a TLS handshake. A TLS handshake uses something called asymmetric encryption, meaning that two different keys are used on the two ends of the conversation. This is possible because of a technique called public key cryptography.
What happens during a TLS handshake?
During the TLS handshake, the two parties generate session keys, and the session keys encrypt and decrypt all communications after the TLS handshake. TLS ensures that the party on the server side, or the website the user is interacting with, is actually who they claim to be.
What is SSL?
SSL stands for Secure Sockets Layer, and it refers to a protocol for encrypting and securing communications that take place on the Internet. Although SSL was replaced by an updated protocol called TLS (Transport Layer Security) some time ago, "SSL" is still a commonly used term for this technology.
How does SSL/TLS work?
These are the essential principles to grasp for understanding how SSL/TLS works:
What is an SSL certificate?
An SSL certificate is a file installed on a website's origin server. It's simply a data file containing the public key and the identity of the website owner, along with other information. Without an SSL certificate, a website's traffic can't be encrypted with TLS.
What is the difference between HTTP and HTTPS?
The S in "HTTPS" stands for "secure." HTTPS is just HTTP with SSL/TLS. A website with an HTTPS address has a legitimate SSL certificate issued by a certificate authority, and traffic to and from that website is authenticated and encrypted with the SSL/TLS protocol.
What is TLS in web?
TLS ensures that the party on the server side, or the website the user is interacting with, is actually who they claim to be. TLS also ensures that data has not been altered, since a message authentication code (MAC) is included with transmissions.
Why is TLS/SSL handshake important?
These keys are important because they interact behind the scenes during website transactions.
How does TLS/SSL work?
The TLS/SSL handshake process 1 Each TLS certificate consists of a key pair made of a public key and private key.#N#These keys are important because they interact behind the scenes during website transactions. 2 Every time you visit a website, the client server and web browser communicate to ensure there is a secure TLS/SSL encrypted connection. 3 When a web browser (or client) directs to a secured website, the website server shares its TLS/SSL certificate and its public key with the client to establish a secure connection and a unique session key. 4 The browser confirms that it recognizes and trusts the issuer, or Certificate Authority, of the SSL certificate—in this case DigiCert. The browser also checks to ensure the TLS/SSL certificate is unexpired, unrevoked, and that it can be trusted. 5 The browser sends back a symmetric session key and the server decrypts the symmetric session key using its private key. The server then sends back an acknowledgement encrypted with the session key to start the encrypted session. 6 Server and browser now encrypt all transmitted data with the session key. They begin a secure session that protects message privacy, message integrity, and server security.
What is TLS/SSL?
TLS/SSL is the standard security technology that works behind the scenes to keep your online transactions and logins secure—here’s how it works . Invisible to the end-user, a process called the “TLS/SSL handshake” creates a protected connection between your web server and web browser nearly instantaneously every time you visit a website.
Why do we need SSL certificates?
TLS/SSL certificates are used to protect both the end users’ information while it’s in transfer, and to authenticate the website’s organization identity to ensure users are interacting with legitimate website owners.
When a web browser (or client) directs to a secured website, the website server shares its TLS?
When a web browser (or client) directs to a secured website, the website server shares its TLS/SSL certificate and its public key with the client to establish a secure connection and a unique session key.