Need of Protection:
- To prevent the access of unauthorized users and
- To ensure that each active programs or processes in the system uses resources only as the stated policy,
- To improve reliability by detecting latent errors.
What are the goals of system protection in operating system?
To prevent the access of unauthorized users and. To ensure that each active programs or processes in the system uses resources only as the stated policy, To improve reliability by detecting latent errors.
What is the goal of protection and security?
Protection is a mechanism to control access to resources. Protection mechanisms provide controlled access by limiting the type of access that various users can make. Security is a measure of confidence that the integrity of a (computer) system relies on. A security system prevents unauthorized access to a system.
What are the 3 goals of operating system?
An operating system has three main functions: (1) manage the computer's resources, such as the central processing unit, memory, disk drives, and printers, (2) establish a user interface, and (3) execute and provide services for applications software.
Why is it important to protect the operating system?
Any vulnerability in the operating system could compromise the security of the application. By securing the operating system, you make the environment stable, control access to resources, and control external access to the environment. The physical security of the system is essential.
What are the goals of protection in operating system differentiate between protection and security?
Protection controls how files and other resources are shared among Operating System users. Security entails the strategy of granting permissions to allow external users access to system resources. Protection deals with the internal threats and malware. Security manages the external threats.
What are the principles of protection?
The principle of protection involves placing a barrier between the pathogen and the susceptible part of the host to shield the host from the pathogen. This can be accomplished by regulation of the environment, cultural and handling practices, control of insect carriers, and application of chemical…
What is the main goal of an operating system?
Primary Goal: The primary goal of an Operating System is to provide a user-friendly and convenient environment.
What are the 4 types of operating system?
64-bit OS and 32-bit OS. Batch OS, Time-Sharing OS, Distributed OS, Real-Time OS, Networking OS.
Which is not the goals of an operating system?
Answer: To keep systems programmers employed is not a goal of a computer's operating system.
How does operating system protect itself?
Modern hardware has features that allow the OS kernel to protect itself from untrusted user code. An executing stream of instructions and its CPU register context. An execution context for thread(s) that provides an independent name space for addressing some or all of physical memory.
What is data protection in operating system?
The term data protection describes both the operational backup of data as well as business continuity/disaster recovery (BCDR). Data protection strategies are evolving along two lines: data availability and data management.
How can the operating system be protected from its environment?
Hardware security includes creating a physical environment in which equipment is protected. Application and operating system software can be protected by using passwords and by eliminating access to those who have no need to use particular software.
What is the purpose of security?
Security purpose means the purpose of preventing shoplifting, fraud, or any other misappropriation or theft of a thing of value, including tangible and intangible goods, services, and other purposes in furtherance of protecting the security or integrity of software, accounts, applications, online services, or any ...
What are the objectives of security?
Security of computer networks and systems is almost always discussed within information security that has three fundamental objectives, namely confidentiality, integrity, and availability.
What is the importance of security in the society?
Safety and security represent many things, including a stable income, consistent housing, clothing, and food supplies as part of the predictability of daily life, protection from crime, and psychological security.
What is the security and safety?
The word safety is used to refer to a condition where someone or a thing is protected from causes that are likely to cause harm. The word security means protecting organisations/people against threats/danger. It is used as a Noun.
What is the role of protection in computer systems?
To improve reliability by detecting latent error s. The role of protection is to provide a mechanism that implement policies which defines the uses of resources in the computer system. Some policies are defined at the time of design of the system, some are designed by management of the system and some are defined by the users ...
What is system protection?
Protection refers to a mechanism which controls the access of programs, processes, or users to the resources defined by a computer system.
Why should application programmer design the protection mechanism?
Application programmer should also design the protection mechanism to protect their system against misuse. Policy is different from mechanism. Mechanisms determine how something will be done and policies determine what will be done.Policies are changed over time and place to place.
Why do we need protection?
To ensure data safety, process and program safety against illegal user access, or even program access, we need protection. It is to ensure that programs, resources and data are accessed only according to the systems’ policies.
What is protection policy?
For that purpose, we have protection policies that are either designed by the system itself or specified by the management itself or are imposed by the programmers individually to protect their programs with extra safety.
How does cryptography protect data?
This helps in transfer of data with full protection. It protects the data by introducing the concept of a key. The key is very important here.
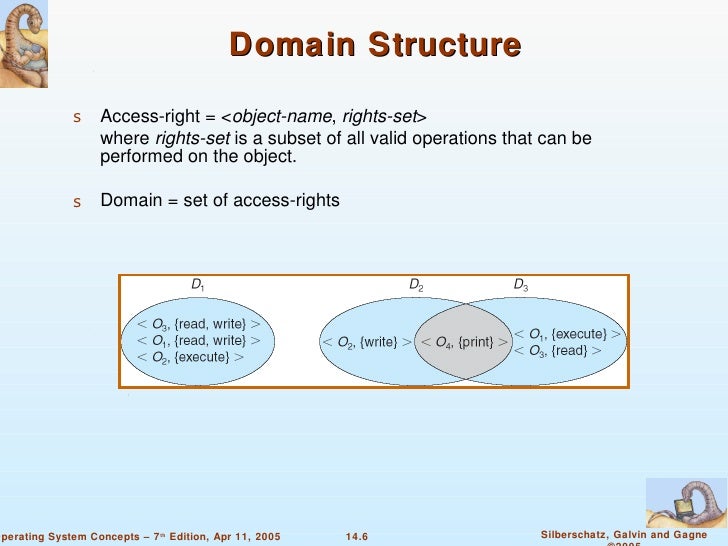
What is the protected domain of a process?
That is the protected domain of a process. A computer system has processes and objects, which are treated as abstract data types, and these objects have operations specific to them. A domain element is described as <object, {set of operations on object}>. Each domain consists of a set of objects and the operations that can be performed on them.
What are security measures?
Security Measures : Security measures at different levels are taken against malpractices, such as no person should be allowed on the premises or allowed access to the systems . The network that is used for the transfer of files must be secure at all times.
What are the policies of a computer?
The policies bind how the processes are to access the resources present in the computer system, resources like CPU, memory, software and even the OS. Both the OS designer and the application programmer are responsible for this. However, these policies always change from time to time.
What is the purpose of a data access policy?
It is to ensure that programs, resources and data are accessed only according to the systems’ policies.
What are the functions of an operating system?
To achieve the goals of an Operating system, the Operating System performs a number of functionalities. They are: Process Management: At a particular instant of time, the CPU may have a number of processes that are in the ready state. But at a time, only one process can be processed by a processor.
What are the two types of goals in an operating system?
There are two types of goals of an Operating System i.e. Primary Goals and Secondary Goal.
What is the responsibility of the Operating System to manage the memory?
So, it is the duty of the Operating System to manage the memory by allocating and deallocating the memory for ...
What is an operating system?
An Operating System is a software that acts as an intermediate between the hardware and the user. It is a kind of resource manager that manages both hardware and software resources of a system. There can be various resources present in the system and to manage it manually is a very very difficult task. So, we make the use of the Operating System ...
Why can't a user give instructions to the hardware?
a user can't directly give instructions to the hardware to perform various operations because it is very difficult for the user to convert its request or instruction into machine language that is used by the hardware components ...
What is I/O device management?
I/O Device Management:There are various I/O devices that are present in a system. Various processes require access to these resources and the process should not directly access these devices. So, it is the duty of the Operating System to allow the use of I/O devices by the various process that are requiring these resources.
Should CPU priority be given to only one process?
The CPU should not give priority to only one process and it should make sure that every process which is in the ready state will be executed. Some of the CPU scheduling algorithms are First Come First Serve, Round Robin, Shortest Job First, Priority Scheduling, etc.
