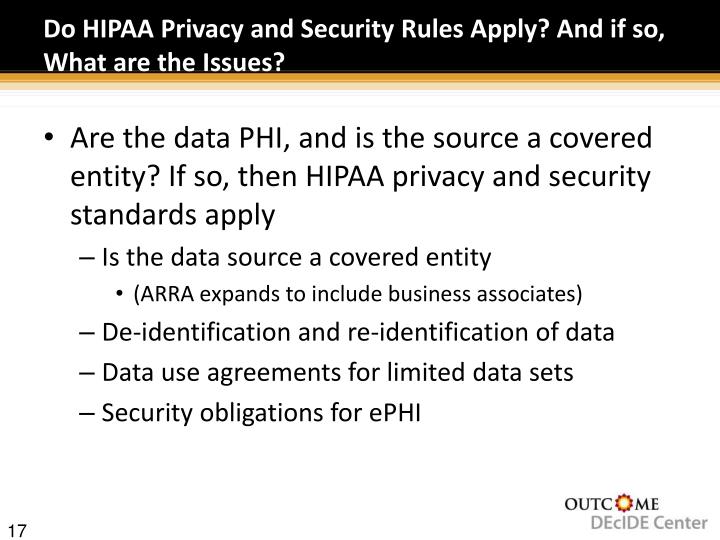
Introduced in 2003, HIPAA Privacy and Security Rules are at the forefront of HIPAA law. The HIPAA Privacy Rule created regulations on how protected health information (PHI) can be used and disclosed. This safeguards PHI to ensure that only authorized individuals have access. It also requires the disclosure of PHI to a patient upon request.
Who must comply with HIPAA privacy standards?
Who must comply with HIPAA privacy standards? As required by Congress in HIPAA, the Privacy Rule covers: Health care providers who conduct certain financial and administrative transactions electronically.
What are the security requirements for HIPAA?
To comply with the HIPAA Security Rule, all covered entities must do the following:
- Ensure the confidentiality, integrity, and availability of all electronic protected health information
- Detect and safeguard against anticipated threats to the security of the information
- Protect against anticipated impermissible uses or disclosures
- Certify compliance by their workforce
What are the three rules of HIPAA regulation?
- Is necessary to prevent fraud and abuse related to the provision of or payment for health care,
- Is necessary to ensure appropriate State regulation of insurance and health plans to the extent expressly authorized by statute or regulation,
- Is necessary for State reporting on health care delivery or costs,
What is the goal of HIPAA Security Rule?
What Is HIPAA Security Rule and Privacy Rule?
- Consequences of Noncompliance. HIPAA requires covered entities including business associates to put in place technical, physical, and administrative safeguards for protected health information (PHI).
- The Privacy and the Security Rules. ...
- Ensuring HIPAA Compliance. ...
See more

What is the HIPAA security rule?
The HIPAA security rule addresses all the tangible mechanisms covered entities must have in place to support internal privacy policies and procedures. Its primary objective is to strike a balance between the protection of data and the reality that entities need to continually improve or upgrade their defenses. So, while the rule covers major concepts like EHRs, it is also designed to be flexible.
What is HIPAA privacy law?
Importantly, the HIPAA privacy law denotes the absence of such restrictions on de-identified patient data, which may be used in research. What the law does cover, however, is PHI in marketing or other uses. Failure to abide can result in HIPAA violation penalties for nurses.
What separates the HIPAA privacy law and security rule?
Examining these differences will set the stage for nurse practitioners to develop a clear and thorough understanding of HIPAA compliance .
What is the theme of HIPAA and nursing?
HIPAA and nursing is the overarching theme, as nurses with a DNP may need to manage compliance from a team perspective, or even a departmental one. Here’s more about what the separate rules entail, and how a doctorate can help improve knowledge.
What is the difference between privacy and security?
At a high level, privacy is related to the disclosure of patient data, whereas security is focused on the actual IT protocols (e.g. passwords and encryption) put in place to safeguard that data. The privacy law, for instance, dictates in which scenarios transmission of patient data is appropriate, like in care coordination. The HIPAA security rule lays out what controls entities subject to it need to maintain to ensure data protection.
What is HIPAA law?
Department of Health and Human Services (HHS), the privacy law was designed to balance the need for data protection, while still allowing for the regulated flow of that information between care professionals.
Why is the security rule needed?
Why is the security rule needed? Health care is one of the industries most vulnerable to cyberattacks like ransomware, and many high-profile data breaches have befallen providers and insurers, leaking the PHI of millions.
What is the HIPAA security rule?
HIPAA Security Rule. The HIPAA Security Rule requires health care companies to take certain preventive measures to protect PHI. It requires businesses to develop and maintain security policies that protect the PHI they create, receive, maintain, or transmit.
What is HIPAA Privacy?
The HIPAA Privacy Rule is a set of requirements put in place by HHS that holds organizations that control Personal Health Information (PHI) responsible for its protection. The HIPAA Privacy Rule establishes national standards to protect individuals’ medical records and other personal health information. The Privacy Rule requires that certain ...
What is protected health information?
Protected health information is protected by the HIPAA Privacy Rule, which includes all “individually identifiable health information” held or transmitted by a covered entity or its business associate, in any form or media, whether electronic, paper, or oral.
Why was HIPAA created?
The HIPAA Privacy Rule was created out of necessity due to the inadequate Federal and State Laws that allowed PHI to be distributed—without either notice or authorization— for reasons that had nothing to do with a patient’s medical treatment or health care reimbursement.
Why is HIPAA important?
The HIPAA Privacy rule was set forth in order to give patients certain rights over their health information, including rights to examine and obtain a copy of their health records and to request corrections.
What are the best ways to comply with HIPAA?
Specifically, HHS recommends the following ten practices to comply with HIPAA Privacy and Security Rules: 1. Email protection systems. 2.
What is the minimum necessary requirement for HIPAA?
HIPAA Minimum Necessary Rule. HIPAA Minimum Necessary is a central component of the HIPAA Privacy Rule that requires covered entities to follow a “minimum necessary” standard for the use and disclosure of PHI. Specifically, the Minimum Necessary standard states that a covered entity must make reasonable efforts to use, disclose, ...
What is the HIPAA security rule?
HIPAA Security Rule. Meanwhile, the HIPAA Security Rule is meant to protect electronic PHI (ePHI). It established national standards on how ePHI is created, received, used, or maintained. The Security Rule requires appropriate safeguards be in place to maintain the integrity, availability, and confidentiality of ePHI.
What is HIPAA compliance?
The Health Insurance Portability and Accountability Act (HIPAA) established several rules that covered entities (CEs) and business associates (BAs) must follow in order to be compliant. View the HIPAA Privacy and Security Rules Summary below.
What are the safeguards for HIPAA?
Healthcare organizations must implement physical, technical, and administrative safeguards. However, the HIPAA Security Rule leaves it up to entities to determine what safeguards are necessary for their organization. Physical Safeguards: protect the physical security of your offices where PHI or ePHI may be stored or maintained.
What is administrative safeguard?
Administrative safeguards should include policies and procedures that document the security safeguards you have in place, as well as employee training on those policies and procedures to ensure that they are being properly executed.
What happens if you don't have PHI?
If your organization is audited by the Department of Health and Human Services (HHS) Office of Civil Rights (OCR), and you don’t have the proper safeguards protecting PHI, you could potentially be facing large fines.
What is protected health information?
Protected health information (PHI) is any individually identifying information on a patient such as name, Social Security number, credit card information, address, and date of birth, to name a few.
What is a covered entity?
A covered entity (CE) is anyone who is directly involved in the treatment, payment, or operations; while a business associate (BA) is a vendor that a CE hires to complete a service, that comes into contact with protected health information (PHI) as part of their job.
What is the privacy rule?
The Privacy rule focuses on the right of an individual to control the use of his or her personal information. Protected health information (PHI) should not be divulged or used by others against their wishes. The Privacy rule covers the confidentiality of PHI in all formats including electronic, paper and oral.
What is the security rule?
The Security rule focuses on administrative, technical and physical safeguards specifically as they relate to electronic PHI (ePHI). Protection of ePHI data from unauthorized access, whether external or internal, stored or in transit, is all part of the security rule. Typically ePHI is stored in:#N#Computer hard drives#N#Magnetic tapes, disks, memory cards#N#Any kind of removable/transportable digital memory media#N#All transmission media used to exchange information such as the Internet, leased lines, dial-up, intranets, and private networks 1 Computer hard drives 2 Magnetic tapes, disks, memory cards 3 Any kind of removable/transportable digital memory media 4 All transmission media used to exchange information such as the Internet, leased lines, dial-up, intranets, and private networks
What is the definition of confidentiality in PHI?
Confidentiality is an assurance that the information will be safeguarded from unauthorized disclosure. The physical security of PHI in all formats is an element of the Privacy rule. The Security rule focuses on administrative, technical and physical safeguards specifically as they relate to electronic PHI (ePHI).
What is the summary of the HIPAA Privacy Rule?
This is a summary of key elements of the Privacy Rule including who is covered, what information is protected, and how protected health information can be used and disclosed. Because it is an overview of the Privacy Rule, it does not address every detail of each provision. Summary of the Privacy Rule PDF - PDF.
What is the purpose of the Privacy Rule?
A major goal of the Privacy Rule is to assure that individuals’ health information is properly protected while allowing the flow of health information needed to provide and promote high quality health care and to protect the public's health and well being.
What is protected health information?
The Privacy Rule protects all "individually identifiable health information" held or transmitted by a covered entity or its business associate, in any form or media, whether electronic , paper , or oral. The Privacy Rule calls this information "protected health information (PHI).".
How often do health plans have to give privacy notice?
Thereafter, the health plan must give its notice to each new enrollee at enrollment, and send a reminder to every enrollee at least once every three years that the notice is available upon request.
When was HIPAA enacted?
Statutory and Regulatory Background. The Health Insurance Portability and Accountability Act of 1996 (HIPAA), Public Law 104-191, was enacted on August 21, 1996. Sections 261 through 264 of HIPAA require the Secretary of HHS to publicize standards for the electronic exchange, privacy and security of health information.
When was the Privacy Rule published?
The Department received over 52,000 public comments. The final regulation, the Privacy Rule, was published December 28, 2000. 2. In March 2002, the Department proposed and released for public comment modifications to the Privacy Rule.
Is a health care provider a covered entity?
These transactions include claims, benefit eligibility inquiries, referral authorization requests, or other transactions for which HHS has established standards under the HIPAA Transactions Rule. 6 Using electronic technology, such as email, does not mean a health care provider is a covered entity; the transmission must be in connection with a standard transaction. The Privacy Rule covers a health care provider whether it electronically transmits these transactions directly or uses a billing service or other third party to do so on its behalf. Health care providers include all “providers of services” (e.g., institutional providers such as hospitals) and “providers of medical or health services” (e.g., non-institutional providers such as physicians, dentists and other practitioners) as defined by Medicare, and any other person or organization that furnishes, bills, or is paid for health care.
What is the HIPAA Privacy Rule?
The Privacy Rule standards address the use and disclosure of individuals’ health information (known as “protected health information”) by entities subject to the Privacy Rule. These individuals and organizations are called “covered entities.”. The Privacy Rule also contains standards for individuals’ rights to understand ...
What is the HIPAA rule?
HIPAA Security Rule. The Health Insurance Portability and Accountability Act of 1996 (HIPAA) is a federal law that required the creation of national standards to protect sensitive patient health information from being disclosed without the patient’s consent or knowledge. The US Department of Health and Human Services (HHS) issued ...
What are the types of entities that are covered by HIPAA?
The following types of individuals and organizations are subject to the Privacy Rule and considered covered entities: 1 Healthcare providers: Every healthcare provider, regardless of size of practice, who electronically transmits health information in connection with certain transactions. These transactions include claims, benefit eligibility inquiries, referral authorization requests, and other transactions for which HHS has established standards under the HIPAA Transactions Rule. 2 Health plans: Entities that provide or pay the cost of medical care. Health plans include health, dental, vision, and prescription drug insurers; health maintenance organizations (HMOs); Medicare, Medicaid, Medicare+Choice, and Medicare supplement insurers; and long-term care insurers (excluding nursing home fixed-indemnity policies). Health plans also include employer-sponsored group health plans, government- and church-sponsored health plans, and multi-employer health plans.#N#Exception: A group health plan with fewer than 50 participants that is administered solely by the employer that established and maintains the plan is not a covered entity. 3 Healthcare clearinghouses: Entities that process nonstandard information they receive from another entity into a standard (i.e., standard format or data content), or vice versa. In most instances, healthcare clearinghouses will receive individually identifiable health information only when they are providing these processing services to a health plan or healthcare provider as a business associate. 4 Business associates: A person or organization (other than a member of a covered entity’s workforce) using or disclosing individually identifiable health information to perform or provide functions, activities, or services for a covered entity. These functions, activities, or services include claims processing, data analysis, utilization review, and billing.
What are covered entities?
The following types of individuals and organizations are subject to the Privacy Rule and considered covered entities: Healthcare providers: Every healthcare provider, regardless of size of practice, who electronically transmits health information in connection with certain transactions.
What is the opportunity to agree or object to disclosure of PHI?
Opportunity to agree or object to the disclosure of PHI (Informal permission may be obtained by asking the individual outright, or by circumstances that clearly give the individual the opportunity to agree, acquiesce, or object)
Who enforces HIPAA rules?
The HHS Office for Civil Rights enforces HIPAA rules, and all complaints should be reported to that office. HIPAA violations may result in civil monetary or criminal penalties. For more information, visit the Department of Health and Human Services HIPAA website. external icon.
Does HIPAA apply to PHI?
The Security Rule does not apply to PHI transmitted orally or in writing. To comply with the HIPAA Security Rule, all covered entities must do the following: Ensure the confidentiality, integrity, and availability of all electronic protected health information.
What is HIPAA security rule?
The HIPAA Security Rule establishes national standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by a covered entity.
What is the NIST HIPAA toolkit?
The NIST HIPAA Security Toolkit Application is a self-assessment survey intended to help organizations better understand the requirements of the HIPAA Security Rule (HSR), implement those requirements, and assess those implementations in their operational environment. A comprehensive user guide and instructions for using the application are available along with the HSR application.
Where is the Security Rule located?
The Security Rule is located at 45 CFR Part 160 and Subparts A and C of Part 164 .