
X.509 is a standard defining the format of public key certificates .An X.509 certificate is a digital certificate that uses the widely accepted international X.509 public key infrastructure (PKI) standard to verify that a public key belongs to the hostname/domain, organization, or individual contained within the certificate.
Full Answer
How to generate digital signature with X509 certificate?
Jul 01, 2020 · An X.509 certificate is a vital safeguard against malicious network impersonators. Without x.509 server authentication, man-in-the-middle attacks can be initiated by malicious access points, compromised routers, etc. X.509 is most used for SSL/TLS connections to ensure that the client (e.g., a web browser) is not fooled by a malicious impersonator pretending to be …
Is it possible to forward a X509 certificate?
X.509 certificates were first released in 1988 as a part of the International Telecommunications Union’s Telecommunication Standardization Sector (ITU-T) and the X.500 Directory Services Standard. In 1993, version 2 was made available, with two additional fields to support directory access control. The latest, version 3, was released in 1996 and defines the formatting used for …
How to create x509 certificates for testing?
In cryptography, X.509 is an International Telecommunication Union (ITU) standard defining the format of public key certificates. X.509 certificates are used in many Internet protocols, including TLS/SSL, which is the basis for HTTPS, the secure protocol for browsing the web. They are also used in offline applications, like electronic signatures .
How to create a X509 certificate using Java?
SSL/TLS X.509 certificates are digital files that are used for Secure Sockets Layer (SSL) or Transport Layer Security (TLS). An SSL/TLS certificate is one of the most popular types of X.509 certificates or a type of public-key certificate which uses the X.509 standard. X.509 certificates contain a public key and the identity of a hostname, organization, or individual.
What is in an x509 certificate?
An X. 509 (also called digital) certificate contains a public key and an identity (a hostname, or an organization, or an individual), and is either signed by a certificate authority or self-signed.
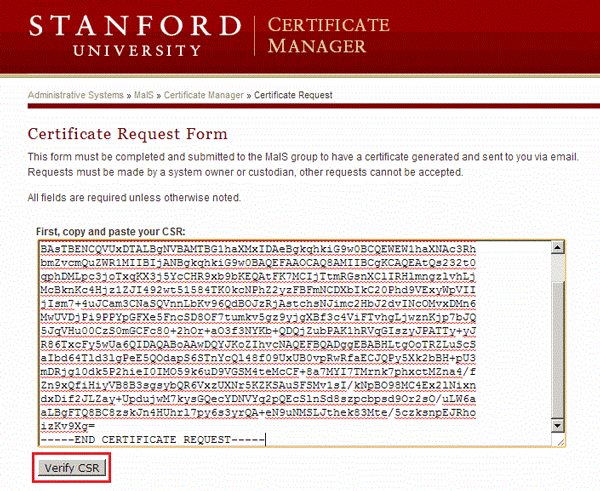
How do I get my x509 certificate?
How do I Get a Certificate?you can create one yourself (using the right tools, such as keytool), or.you can ask a Certification Authority to issue you one (either directly or using a tool such as keytool to generate the request).
Is x509 a SSL certificate?
SSL/TLS X. 509 certificates are digital files that are used for Secure Sockets Layer (SSL) or Transport Layer Security (TLS). An SSL/TLS certificate is one of the most popular types of X. 509 certificates or a type of public-key certificate which uses the X.
How do I know if my certificate is x509?
If the certificate is in text format, then it is in PEM format.You can read the contents of a PEM certificate (cert.crt) using the 'openssl' command on Linux or Windows as follows:openssl x509 -in cert.crt -text.If the file content is binary, the certificate could be either DER or pkcs12/pfx.More items...
Does x509 certificate contains private key?
An X. 509 certificate consists of two keys, namely a public key and a private key. This key pair, depending upon the application, allows you to sign documents using the private key so that the intended person can verify the signature using the public key related to it.
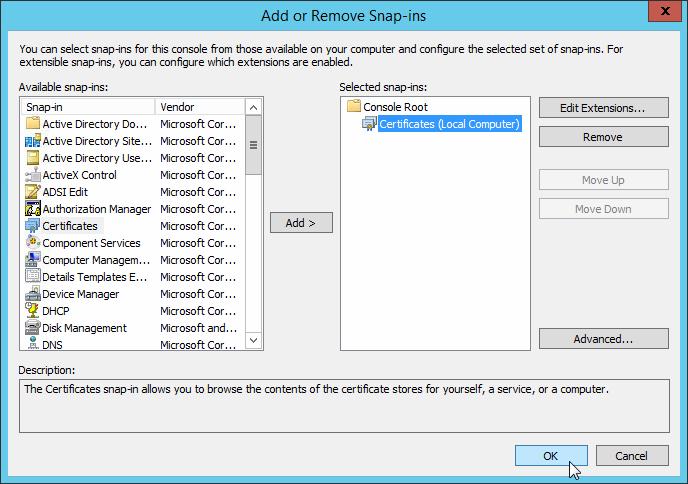
Where are x509 certificates stored?
Certificates stores are kept in the system registry under the keys HKEY_LOCAL_MACHINE\Software\Microsoft\SystemCertificates and HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates. Each user has a MY certificate store which contains his/her personal certificates.
Certificate fields
Over time there have been three certificate versions. Each version adds fields to the one before. Version 3 is current and contains version 1 and version 2 fields in addition to version 3 fields. Version 1 defined the following fields:
Certificate formats
Certificates can be saved in a variety of formats. Azure IoT Hub authentication typically uses the PEM and PFX formats.
Next steps
If you want to generate test certificates that you can use to authenticate devices to your IoT Hub, see the following topics:
What is X509 verification?
As part of the X.509 verification process, each certificate must be signed by the same issuer CA named in its certificate. The client must be able to follow a hierarchical path of certification that recursively links back to at least one root CA listed in the client’s trust store.
What is X509 used for?
X.509 is most used for SSL/TLS connections to ensure that the client (e.g., a web browser) is not fooled by a malicious impersonator pretending to be a known, trustworthy website. Securing Internet communications. Securing intranet communications. Securing email communications. Securing device communications.
How many root certificates does Firefox have?
For example, at the current time of writing, the Firefox trust store holds 150 root certificates that are automatically trusted by their web browser. In contrast, Google Chrome uses the underlying OS’s trust store to determine whether a certificate is trusted, with a few exceptions.
Why is X509 important?
As mentioned by Gartner, X.509 certificates are critical to establish digital trust in the digital world. Without proper management of these certificates, security teams leave their company open to outages, breaches, and failed audits.
What is a DER certificate?
DER is the most popular file format to store X.509 certificates. DER-encoded certificates are binary files and cannot be read by text editors, but they can be processed by web browsers and some applications without any problems.
When was X.509 published?
In 1988 , X.509 version 1 was published. The hierarchical arrangement of the distinguished names followed the rules for X.500. These rules were inspired by the systems used to assign telephone numbers globally.
Does X509 need to be validated?
Only the server needs to be validated in most secure browsing sessions. Client authentication is less common but would require the server to verify the client’s certificate as well. The X.509 certificate’s signature must be verified by the client before establishing an HTTPS connection.
What is X509 certificate?
An X.509 certificate consists of information related to the party to which a certificate is issued and the identity that issued it (certificate authority). Standard information in an X509 certificate includes:
Why use X509?
X.509 certificates are used for two primary reasons: To verify the identity of a website, individual or an organization. In other words, they let users know that the person/organization really is who they say they are. To protect data against man-in-the-middle (MitM) attacks through the use of asymmetric encryption.
What is the validity period of a certificate?
Validity period of the certificate — The period during which certificate is valid to use. Subject distinguished name — The name of the identity the certificate is issued to (individual, organization, domain name, etc.) Subject public key information — The public key of the certificate.
When was the X.509 certificate released?
X.509 certificates were first released in 1988 as a part of the International Telecommunications Union’s Telecommunication Standardization Sector (ITU-T) and the X.500 Directory Services Standard. In 1993, version 2 was made available, with two additional fields to support directory access control. The latest, version 3, was released in 1996 ...
What is digital signature?
Digital Signature. A digital signature is added by certificate authority (CA) to assure users that the certificate in use is genuine. In other words, digital signature provides the proof that the certificate you have been given is the exact certificate issued by a trusted CA to the website in question.
What is an X.509 Certificate and Why is it Important?
An X.509 certificate is a widely used digital certificate format based on asymmetric cryptography. Each certificate uses a pair of encryption keys known as the public and private key.
Why Use X.509 Certificates?
Certificates offer a range of solid security benefits to those who implement them. The main benefit, however, is that they take the place of passwords in authentication. In other words, they grant secure, passwordless access to resources like Wi-Fi and VPNs.
Implementing X.509 Certificates
You can’t simply conjure an X.509 certificate alone out of the ether. Each certificate is issued to a device or user by a CA, which is an integral part of a Public Key Infrastructure (PKI).
The New Golden Standard of Network Security: Certificate-Based Authentication
Passwords are a significant attack vector in the modern era. Ditching them entirely with certificate-based authentication greatly increases the security of your network. As an extra benefit, users also get to enjoy the convenience of passwordless authentication.
What is X.509 certificate?
X.509 certificates are used in many Internet protocols, including TLS/SSL, which is the basis for HTTPS, the secure protocol for browsing the web. They are also used in offline applications, like electronic signatures. An X.509 certificate contains a public key and an identity (a hostname, or an organization, or an individual), ...
When was the X.509 issued?
X.509 was initially issued on July 3, 1988, and was begun in association with the X.500 standard. The first tasks of it was providing users with secure access to information resources and avoiding a cryptographic attack « Man-in-the-middle attack ».
What is a certificate chain?
A certificate chain (see the equivalent concept of "certification path" defined by RFC 5280 section 3.2) is a list of certificates (usually starting with an end-entity certificate) followed by one or more CA certificates (usually the last one being a self-signed certificate), with the following properties:
What is RFC 5280?
RFC 5280 (and its predecessors) defines a number of certificate extensions which indicate how the certificate should be used. Most of them are arcs from the joint-iso-ccitt (2) ds (5) id-ce (29) OID. Some of the most common, defined in section 4.2.1, are:
How does a digital signature work?
Digital signature systems depend on secure cryptographic hash functions to work. When a public key infrastructure allows the use of a hash function that is no longer secure, an attacker can exploit weaknesses in the hash function to forge certificates. Specifically, if an attacker is able to produce a hash collision, they can convince a CA to sign a certificate with innocuous contents, where the hash of those contents is identical to the hash of another, malicious set of certificate contents, created by the attacker with values of their choosing. The attacker can then append the CA-provided signature to their malicious certificate contents, resulting in a malicious certificate that appears to be signed by the CA. Because the malicious certificate contents are chosen solely by the attacker, they can have different validity dates or hostnames than the innocuous certificate. The malicious certificate can even contain a "CA: true" field making it able to issue further trusted certificates.
Is a self signed root certificate untrusted?
Validation of the trust chain has to end here. If the validating program has this root certificate in its trust store, the end-entity certificate can be considered trusted for use in a TLS connection. Otherwise, the end-entity certificate is considered untrusted.
Does CA1 have a public key?
In order to manage that user certificates existing in PKI 2 (like "User 2") are trusted by PKI 1, CA1 generates a certificate (cert2.1) containing the public key of CA2. Now both "cert2 and cert2.1 (in green) have the same subject and public key, so there are two valid chains for cert2.2 (User 2): "cert2.2 → cert2" and "cert2.2 → cert2.1 → cert1".
What is X.509 certificate?
What Is an SSL/TLS X.509 Certificate? SSL/TLS X.509 certificates are digital files that are used for Secure Sockets Layer (SSL) or Transport Layer Security (TLS). An SSL/TLS certificate is one of the most popular types of X.509 certificates or a type of public-key certificate which uses the X.509 standard.
What happens if a certificate is expired?
If the information does not match, or the certificate has expired, the browser displays an error message or warning. In addition, many browsers now flag all sites using HTTP as insecure. If the certificate has expired, the web browser will display an error message or warning.
Is SSL certificate reliable?
An SSL/TLS certificate is most reliable when issued by a trusted Certificate Authority (CA). The CA has to follow very strict rules and policies about who may or may not receive an SSL Certificate. So, when you have a valid SSL Certificate from a trusted CA, there is a higher degree of trust. When a certificate authority (CA) ...
What is X509 certificate?
X509 certificates act as a digital passport. The information and data present in the X509 certificate are only about you and no one else. A similar type of authority like Certificate authority (CA) also exists for X509 certificates. The Certificate authority (CA) helps to make the privacy of your identity from the third party.
When was the X509 certificate created?
X509 BRIEF HISTORY. The X509 certificate was created in 1988. It is a part of the series X500 directory. In today’s time, this certificate helps in identifying the personal identity with a secure connection.
Which hierarchy verifies the validity of the certificate issuer?
The hierarchy that verifies the validity of the certificate issuer is the X509 certificate. The SSL certificate is the main that tells about the legitimacy of the browser. On the other hand, there are root certificates that are the basic certificates and include the certificate authority signature.
What is CA in digital signature?
This will help to identify that the user is genuine or not. The main aim is that it proves the certificate which is issued to the user by the certificate authority (CA) is real and ensure the website as well.
Is SSL a root certificate?
The SSL certificate and root certificates are not connected with each other and some gap appears between the two. These intermediate certificates fill this gap. They all together form a chain of certificates from SSL to the intermediate following root certificate. It contains the signature from all the entities.
Certificate Fields
- To review the contents of a typical X.509 certificate in the wild, we will examine www.ssl.com’s SSL/TLS certificate, as shown in Google Chrome. (You can check all of this in your own browser for any HTTPS website by clicking the lock on the left side of the address bar.) 1. The first grou…
Certificate Formats
For More Information
Next Steps
- Over time there have been three certificate versions. Each version adds fields to the one before. Version 3 is current and contains version 1 and version 2 fields in addition to version 3 fields. Version 1 defined the following fields: 1. Version: A value (1, 2, or 3) that identifies the version number of the certificate 2. Serial Number: A unique number for each certificate issued by a CA …
What Is An X.509 Certificate and Why Is It Important?
- Certificates can be saved in a variety of formats. Azure IoT Hub authentication typically uses the PEM and PFX formats.
Why Use X.509 Certificates?
- For more information, see the following topics: 1. The layman’s guide to X.509 certificate jargon 2. Conceptual understanding of X.509 CA certificates in the IoT industry
Implementing X.509 Certificates
- If you want to generate test certificates that you can use to authenticate devices to your IoT Hub, see the following topics: 1. Using Microsoft-Supplied Scripts to Create Test Certificates 2. Using OpenSSL to Create Test Certificates 3. Using OpenSSL to Create Self-Signed Test Certificates If you have a certification authority (CA) certificate or subordinate CA certificate and you want to u…
The New Golden Standard of Network Security: Certificate-Based Authentication
- An X.509 certificate is a widely used digital certificate format based on asymmetric cryptography. Each certificate uses a pair of encryption keys known as the public and private key. In a nutshell, the private key on a certificate can generate encryption that can only be decrypted by its public key partner. The private key is kept by the certificate holder while the public key can b…